The longest key ever publicly broken by exhaustive key search has 64 bits. A challenge I created a few years ago aims to improve this world record by one bit.
Click here for the complete top 50 list
In September 2002 the media reported about a 64 bit cryptographic key that had been cracked by exhaustive search (i.e., brute force).
This news came as no surprise, as five years earlier a 56 bit key had been broken the same way. In both cases computer users all over the world had provided unused processor capacity for testing key candidates. No less than 331,252 users participated to break the 64 bit key. After 1757 days (almost five years), a participant in Japan finally discovered the correct candidate.
The RSA Challenges (1997-2007)
Both the organizers of the 56 and the 64 bit key search started their projects in order to win an award endowed by the US company RSA Security (RSA Challenges). In fact, RSA Security paid both winners a prize money of $10,000. There were several more secret key challenges created by RSA Security, each with a $10,000 award.
The logical next step would have been to break the 72 bit key challenge. However, in May 2007 RSA Security announced the termination of all challenges. As the ciphertexts are still available and the solutions not known, you still can try to break the keys. However, there is no prize money any more.
Since the breaking of the 64 bit key in 2002, nobody has claimed to have cracked a longer key than this one by exhaustive search. This means that 64 bit are the current world record.
The World Record Challenge
In 2010 I decided to set up a secret key challenge aiming to improve the current world record by one bit. I published this challenge on the crypto puzzle platform MysteryTwister C3. There’s also a German version of it.
To my regret, there is no prize money. However, chances are good that there will be a broad media echo if this world record is improved after such a long time.
The ciphertext I took was encrypted with CrypTool. I used the AES encryption algorithm in ECB mode with a key length of 128 bits. The first 65 bits must be guessed. The remaining 63 bits are set to 1.
The first eight bytes of cleartext represent the solution of the challenge. They form an English word written in capital ASCII letters. The remaining eight bytes have the value „CrypTool“ (in ASCII code) or 43 72 79 70 54 6F 6F 6C (in hex code).
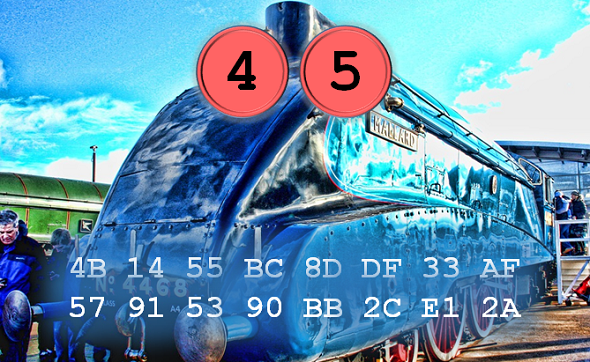
Here is the ciphertext of the World Record Challenge (in hex code):
4B 14 55 BC 8D DF 33 AF 57 91 53 90 BB 2C E1 2A
This challenge is certainly a tough one – after all, solving it means a new world record. However, as computer technology has considerably improved within the last 15 years, it should be possible to find the solution in much less than five years. If we assume that computation power doubles every 18 months (Moore’s law), the time needed will be a thousand times less. Instead of five years (~ 1800 days) this would mean 1.8 days, provided that the same amount of hardware is used.
After 15 years it is time to improve this record. I wish you good luck trying it!
Follow @KlausSchmeh
Further reading: How to Use a Rubik’s Cube for Encryption
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/




Kommentare (14)