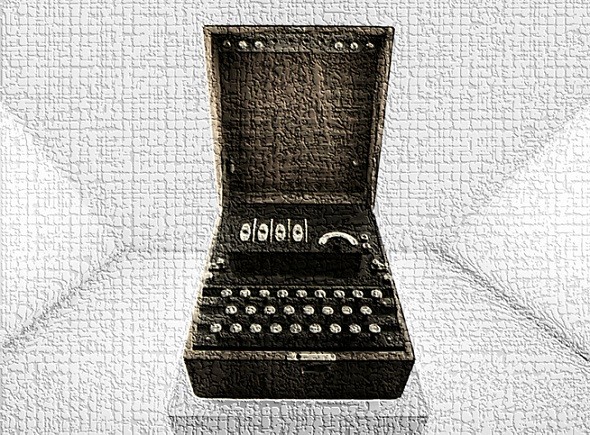
On Friday the Heinz Nixdorf Museum will broadcast a number of radio messages encrypted with an Enigma. Codebreaking experts in Bletchley Park will try to decipher these cryptograms with WW2 technology. Enigma experts will try the same with computer support.
Breaking Enigma messages has a long history. Already in the 1930s, Polish mathematicians Marian Rejewski, Henryk Zygalski and Jerzy Różycki deciphered German Enigma ciphertexts.
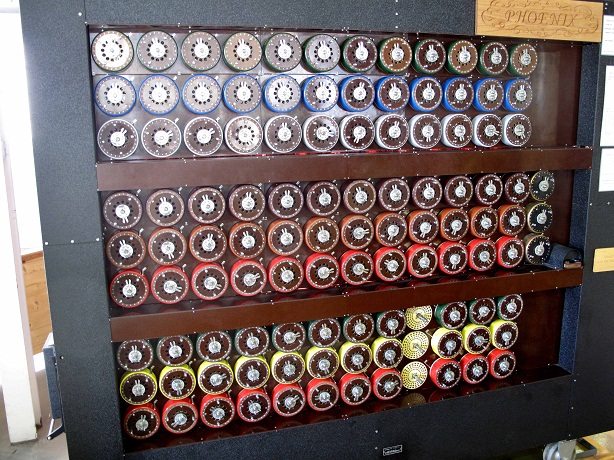
Based on the Polish expertise, British codebreakers later developed a codebreaking machine, the Bombe (also known as Turing-Welshman Bombe), which enabled them to read hundreds of thousands of German Enigma messages during World War II.
In order to support their British colleagues, US codebreakers built a number of Bombes, too. Their task was to break the four-rotor Naval Enigma, which was especially hard to decipher.
After the end of WW2 the Enigma was hardly used any more. Breaking Enigma messages became obsolete. Most copies of the Bombe were disassembled. For decades the work on methods for deciphering the Enigma came to a halt.
Enigma codebreaking with the computer
From the late 1970s on historians became more and more interested in the Enigma. It turned out that this machine had influenced the course of WW2 in a considerable way. The Enigma now also got into the focus of cryptology experts. In 1995 Jim Gillogly, a reader of this blog, described a new computer-based ciphertext-only attack on Enigma messages.
In 2004 Frode Weierud and Geoff Sullivan, two more readers of this blog, started a project named “Breaking German Wehrmacht Ciphers“, in the course of which they solved hundreds of original Enigma messages from the Flossenbürg concentration camp and Hitler’s Russia campaign. Earlier this year, Frode Weierud and Olaf Ostwald published a paper titled Modern breaking of Enigma ciphertexts in the scientific magazine Cryptologia. This article reports on further improvements in Enigma codebreaking with modern means.
In 2006 musician Stefan Krah along with hundreds of supporters, who provided computer capacity, cracked three World War II enigma codes.
Michael Hörenberg, a teacher from Southern Germany, and Dan Girard have been very successful in breaking Enigma messages, too. Michael’s website renders a lot of interesting information about his and Dan’s codebreaking activities.
All in all, breaking Enigma messages has made considerable progress in the last 15 years. Not only have computers improved, but Enigma codebreaking algorithms have also become more and more sophisticated.
The Cipher Event
On Friday, April 7, Enigma codebreaking experts will have the chance to proof their abilities. The HeinzNixdorf MuseumsForum (HNF) in Paderborn, Germany, and the Bletchley Park Museum in UK (Bletchley Park is the place where the British broke the Enigma) will organize a cryptographic puzzle game they call Cipher Event (thanks to Karsten Hansky, Roland Wintgen, Ralf Bülow, and Tomtoo for the hint).
Starting at 9 a.m., the HNF will send radio messages that are encrypted with an original Enigma. Radio amateurs are encouraged to listen to these messages (40m, 7036 kHz, DL0HNF) and to write them down. Codebreaking experts in Bletchley Park will try to decipher these cryptograms with a Bombe (as no original copy of this machines has survived, a rebuild will be used).
In addition to the codebreakers in Bletchley Park, other Enigma experts are invited to break the radio messages coming from Paderborn. I am sure, some of the Enigma deciphering specialists mentioned above will take part in this challenge. They will probably be a lot faster than the guys in UK, as they will use computers instead of WW2 equipment. If you have deciphered one of the messages, send the solution to enigma(at)hnf.de.
If you happen to be in Paderborn or Bletchley Park, you can watch the sending or breaking activities onsite. Otherwise you have the chance to follow the live stream on the HNF website.
One of the purposes of the Cipher Event is to honor Alan Turing, who was the mastermind of the Enigma breaking in Bletchley Park. If you want to meet Alan Turing’s nephew Dermot Turing, you should come to the Euro HCC in Bratislava. Dermot will give a keynote speech there.
Follow @KlausSchmeh
Further reading: The mystery of the Soyuz files
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/



Kommentare (18)