A French museum has an unusual cipher device on display. Can my readers find out how it works?
Last week I learned something new about geography, when I wrote about an encrypted postcard sent from the Isle of Wight (blog reader Thomas Bosbach solved it, by the way). For today’s blog post I had to inform myself about history, namely the person of French king Henry II (1519–1559).
As it turned out, I had read about this guy before, but not in a crypto history book but in a biography of French astrological writer Nostradamus, written by my friend Bernd Harder, who has been the spokesman of the German skeptics society for many years.
Henry II and Nostradamus
As Bernd wrote, Henry’s wife, Catherine de’ Medici, was one of Nostradamus’s greatest admirers. She summoned him to Paris to draw up horoscopes for her family. Henry died in 1559 during a jousting match, when he was wounded in the eye by a fragment of the splintered lance of his opponent. Later, some considered the following lines written by Nostradamus as a prophecy of Henry’s death:
The young lion shall overcome the older one,
on the field of combat in single battle,
He shall pierce his eyes in a golden cage,
Two forces one, then he shall die a cruel death.
In fact, the expression “pierce his eyes” seems to fit quite well (though only one eye was hit). However, everything else told in this four-liner (Nostradamus published hundreds of them) is much less convincing. Henry II was never referred to as lion. He did not die during a battle or on a battlefield. He didn’t wear a golden “cage” (helmet).
Henry’s cipher device
The reason why I write about Henry II today is, of course, not his relationship to Nostradamus (though the many alleged codes found in the works of Nostradamus are perfect examples of pseudo-steganography), but his relationship to cryptology. As far as I know, there is no mention of Henry II in the crypto history literature. However, my American cryptographer friend Tony Patti …
… made me aware of the following picture of a cipher device that is available on Wikipedia/Wikimedia:
Source: Uploadalt
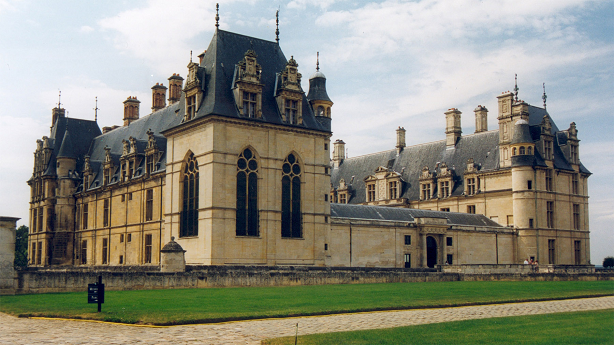
According to the description given on Wikimedia, this item is a 16th century French cipher machine in the shape of a book with arms of Henry II. A crypto history expert would certainly not call it a cipher machine, but a cipher device. It is located in the Renaissance Museum in the castle of Écouen, north of Paris (it is now included in my Cryptologic Travel Guide).
Source: Sir Gawain
Henry’s cipher device looks quite luxurious, so it can easily be imagined that it was used by a king. The device features 20 rings (five more might be missing). The purpose of the device might have been to conduct a polyalphabetic encryption – which would be quite unusual for the 16th century. I wonder why there are two different kinds of rings on the right side.
To my regret, I don’t have any additional information about this cipher device. Especially, I don’t know how it worked. If a reader can find out more about this unusual item, please leave a comment.
Follow @KlausSchmeh
Further reading: Who knows the encryption device ACP 212?
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/






Kommentare (2)