
Bernard Fabrot (used with permission)
The solution of LCS35 has received considerable media coverage. Among others, Wired (English) and Golem (German) have published articles about it. I have never heard of Bernard Fabrot before. I don’t think he has ever been active in the crypto scene. However, he is not a no-name, as he has written a couple of Linix books in French.
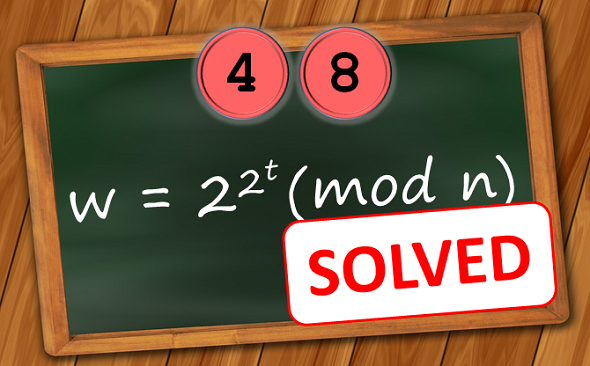
Instead of 35 years, as expexted by Rivest, Fabrot needed only three-and-a-half years for solving LCS35. As it seems, he was only about two weeks faster than a US group named Cryptophage, who worked on the LCS35 challenge, too.
For his computations, Fabrot used the GNU Multiple Precision Arithmetic Library, a free software library written in C for doing precise arithmetic. Fabrot dedicated one of the CPU cores on his home PC to solve the challenge. Wired quotes him: “During all these years I told no one I was trying to solve the puzzle except very close friends. I knew I had a chance, but if I told anyone they could have used a more powerful CPU to overtake me.”
The solution, i.e., the value of w and the plaintext, will be published on May 15th.
Edited to add: Meanwhile I have established contact with Bernard. I will ask him for details.
Follow @KlausSchmeh
Further reading: The Top 50 unsolved encrypted messages: 45. The World Record Challenge
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (1)