An encrypted telegram sent by two Russian communists in 1918 allegedly reports the death of czar Nicholas II and his family. Can a reader decipher it?
Once again, I have found an interesting encrypted message via Google. When I searched for “encrypted telegram”, a link to a Pinterest site titled Romanov Obsession came up. “Romanov” is the name of an old Russian aristocratic family, the most famous members of which were czar Nicholas II (1868-1914) with his wife and children. Romanov Obession provides a collection of pictures related to these persons.

Source: commons.wikimedia.org/wiki/File:Russian_Imperial_Family_1913.jpg
Nicholas II and his wife Alexandra had four daughters and a son. One of the daughters, Olga, kept a diary that was partially encrypted. I blogged about this story in 2016 (in German).
As is well known, the Romanov family was imprisoned by the communists after the February Revolution. All five were shot and bayoneted to death in Yekaterinburg on the night of 16–17 July 1918.
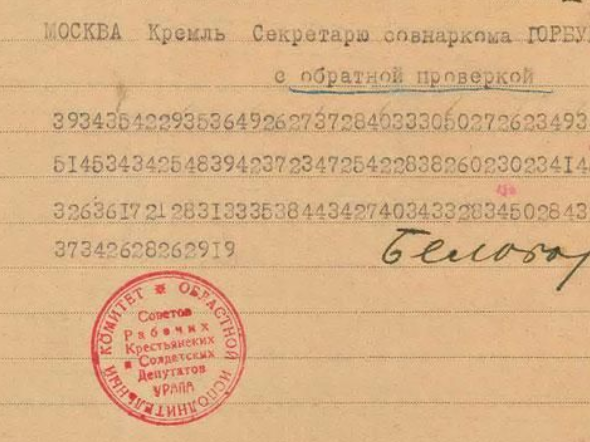
According to Romanov Obsession, the two communists Alexander Beloborodov and Filipp Goloshchekin sent the following telegram to fellow-communist Yakov Sverdlov after the killing:
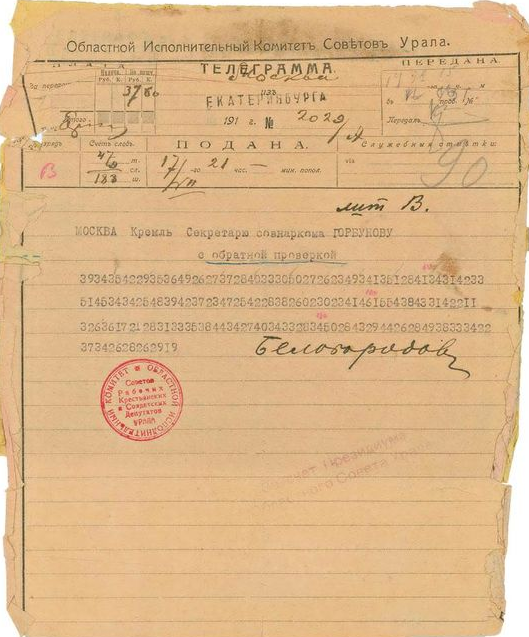
Romanov Obsession
Wikipedia mentions an encrypted message that is probably identical with this one. Translated to English, it read: “Inform Sverdlov the whole family have shared the same fate as the head. Officially, the family will die at the evacuation.”
There is no further information about this telegram in the literature known to me. Even in David Kahn’s The Codebreakers, which contains a whole chapter about Russian cryptography, this message isn’t mentioned.
So, I’m asking myself which encryption method was used. The ciphertext consists of long number sequences without any spaces in between. My guess is that these sequences have to be interpreted as two-digit nubers, most of which are smaller than 50. If this assumption is correct, the encryption system used could be a (small) nomenclator. Perhaps, the low numbers stand for letters, while the higher ones represent names.
The most popular encryption method used for telegrams were codebook codes. However, this ciphertext doesn’t look like a codebook cryptogram to me. Especially, it would be very untypical for such a code that (with few exceptions) every second digit is smaller than six.
Can a reader say more about this telegram?
Follow @KlausSchmeh
Further reading: Revisited: An encrypted telegram from Mount Everest
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (5)