How Matthew Brown solved the encrypted telegrams of Canada’s first prime minister
Canada’s first prime minister left numerous coded telegrams and other encrypted messages. Blog reader Matthew Brown was able to decode most of them – but not all.
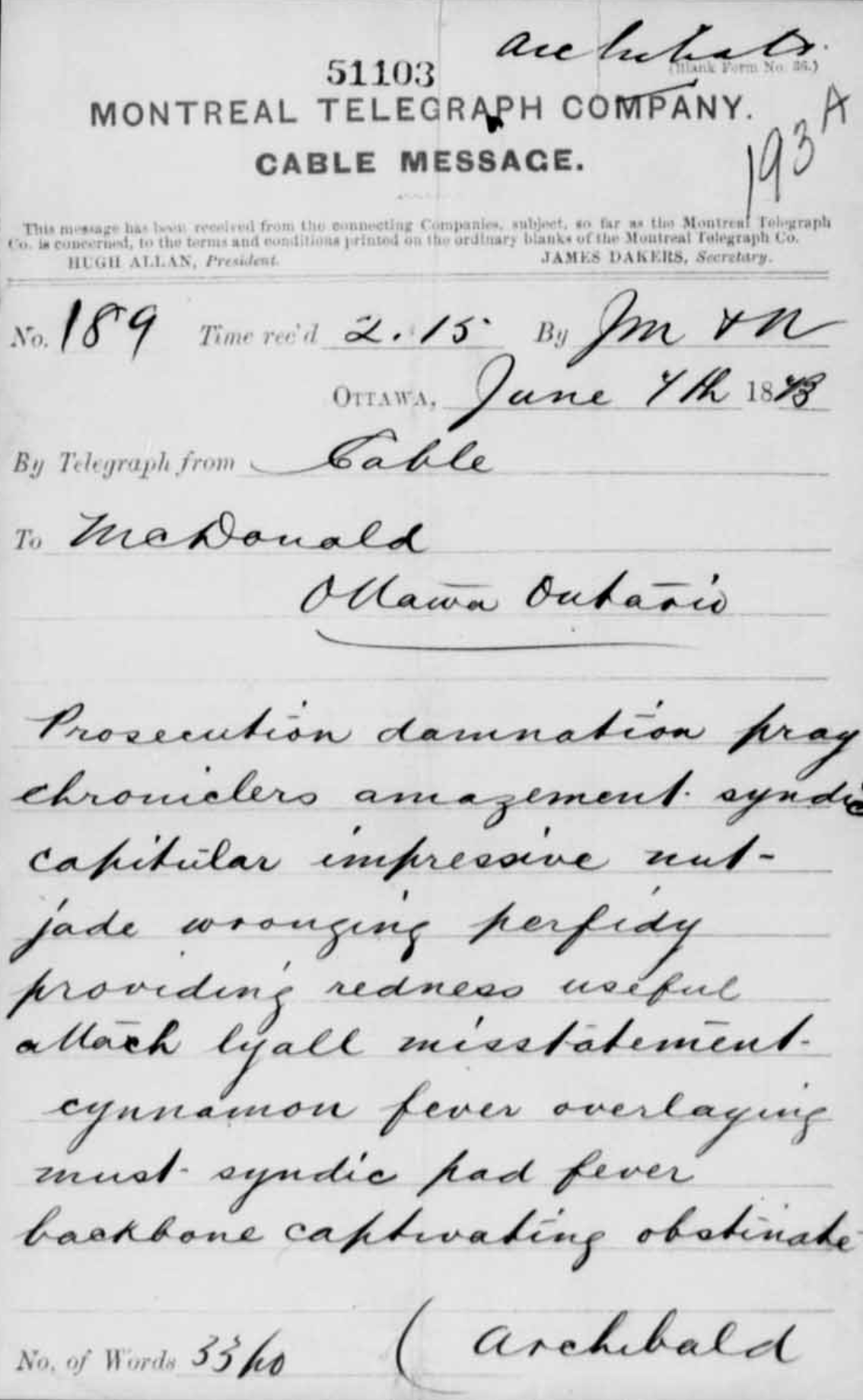
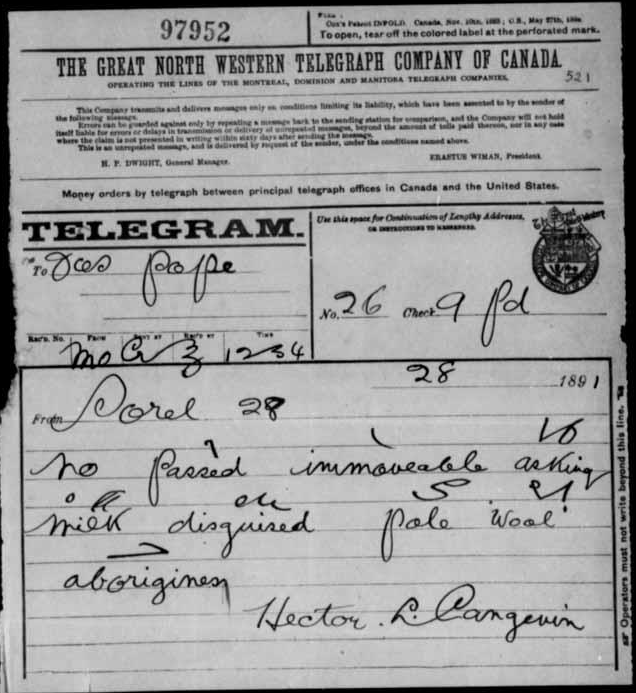
John A. Macdonald (1815-1891) was the first Canadian prime minister. Blog reader Matthew Brown from England has brought to my attention a collection of coded messages (mainly telegrams) that Macdonald sent or that originated around him. These messages come from Canadian archives and are accessible through the “Canadian Library and Archives” website. Here is an example (it is the first entry in the list presented below):
Here is a transcription:
Prosecution damnation pray chronicler amazement syndic capitular impressive nut jade wronging perfidy providing redness useful? lyall misstatement cinnamon fever overlaying must syndic had fever backbone captivating obstinate
As can be seen, this telegram consists of meaningful words (“damnation”, “pray”, “fever”, …), but these do not form meaningful sentences. The probable reason: Macdonald used a codebook. Codebooks, as well as telegrams encoded with them, were widely used at the time.
A codebook translates every common word of a language into code words (also called a “code group”). Code words were often numbers (such as “738392”) or groups of letters (such as “hsszdh”). But meaningful words were also used.
Solution
How to crack such a codebook encryption? Readers of this blog or my book “Codebreaking: A Practical Guide” may know that there is often only one method that leads to success: You track down the codebook. Satoshi Tomokyo and John McVey’s websites list and link to numerous codebooks. You can also find them on Google Books and in the Internet Archive.
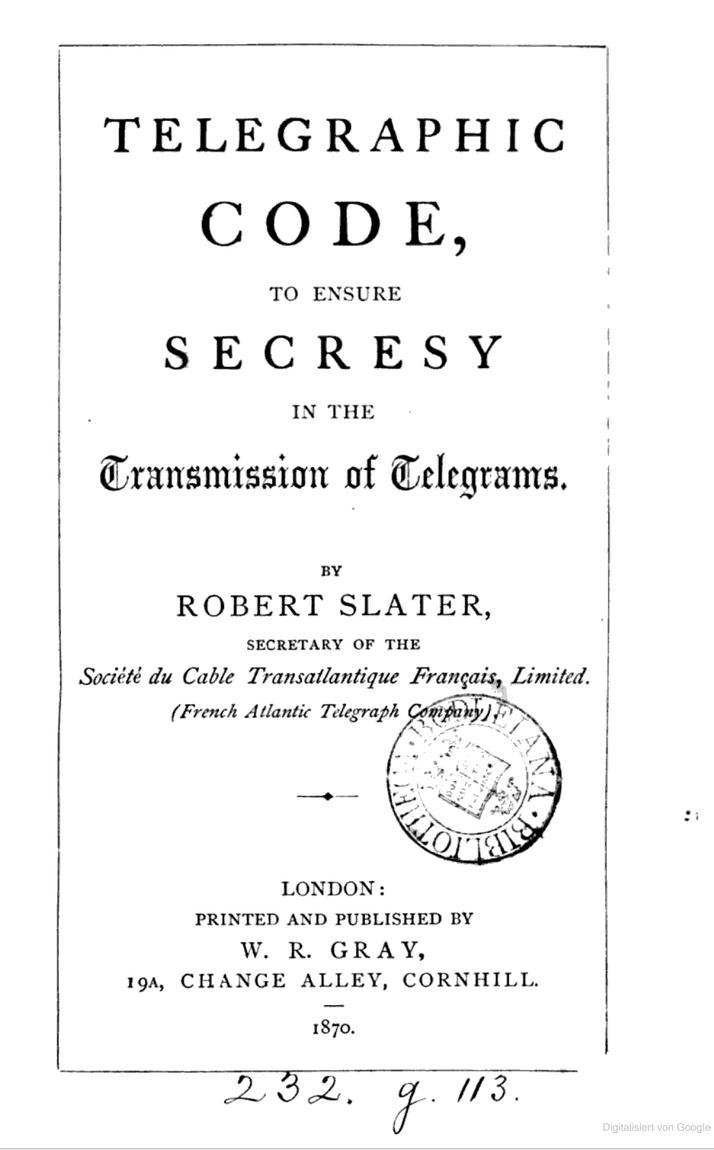
In this case, however, no search was necessary at all. Matthew Brown had already found the solution before the problem arose: When he looked at the Slater codebook (from 1870), which is available on Google Books, he read that the Canadian government had once worked with it. Only after that did he look in the Canadian archives and find the cryptograms in question. The following picture shows the title page of the Slater codebook:
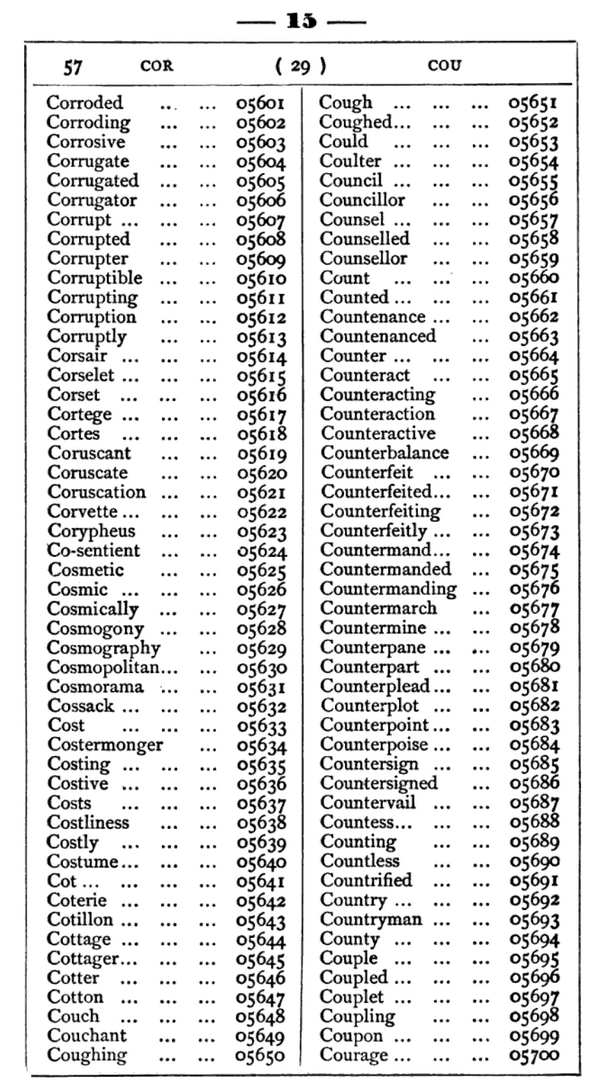
Here is a page from the Slater codebook:
However, things were not quite that simple. As you can see, the Slater code maps English words to numbers. By the way, each five-digit number must be preceded by the number above the table, which assigns CORRODED the code word 1505601. However, Macdonald could not have used the codebook in this form, because his messages consist not of numbers but of words.
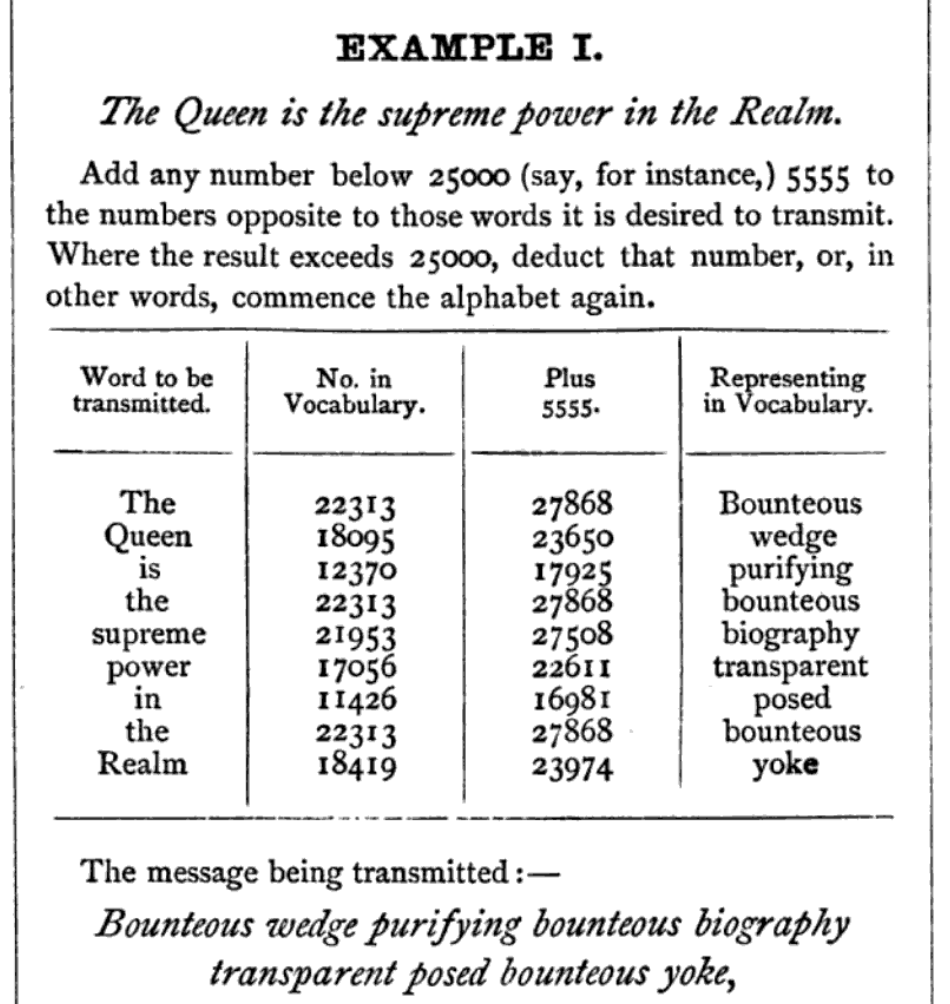
In fact, the introduction to the codebook explains how to use the code in a different way: One chooses the word one is looking for, takes the associated number, adds an agreed number, and finally converts the result back to the associated word. The agreed number is a key that must be known only to the sender and receiver. The following table shows how the phrase THE QUEEN IS THE SUPREME POWER IN THE REALM is encrypted using the key 5555:
The encrypted message reads: BOUNTEOUS WEDGE PURIFYING BOUNTEOUS BIOGRAPHY TRANSPARENT POSED BOUNTEOUS YOKE
Matthew Brown’s solution
Matthew Brown assumed that John A. Macdonald and his colleagues had also encrypted in this way. But which key(s) had they used? Since the Slater codebook has 25,000 entries, there were 24,999 possibilities.
Matthew wrote a computer program that applied each of the nearly 25,000 possible keys to an encrypted message, checking in each case whether the plaintext made sense. The program decided the latter by evaluating the frequencies of words in the plaintext in the English language. Frequent words, such as MONEY or GERMANY, yielded higher scores than, say, CANTATA or REPULSIVE.
In fact, Matthew was able to decode most of the encrypted messages from Macdonald’s environment in this way. He thankfully provided me with a list of all the cryptograms with transcription, link to the archive, and (if known) the plaintext. For example, the telegram shown at the beginning was encrypted with the key 250 and reads in plaintext as follows:
PRIVATE CRITICAL POINT CHANCEs AGAINST SUCCESS BUT IF NEGOTIATION INTERRUPTED WHEN PARTY PROFESS READINESS UNDERTAKE? ALAN MIGHT CHARGE FAILURE ON MOLLIFY SUCCESS GRAND FAILURE ASSURED BY NINETEENTH
As another example, let’s look at number 10 on the list:
Matthew’s transcription reads as follows:
Hay Renouncing beautifully parallel curly rumbled hug heligoland trustee speak
Here Matthew determined the key 500 and the following plain text:
GORGE RECEIVED ASSURANCE OF CORDIAL RESPONSE RESPECTING YOUR TEETOTALER SISTER
As Matthew found out, the senders initially used multiples of 100 as keys. Since there are 100 words on a page in the Slater codebook, this makes encryption easier. From about 1888, the date was added to the key, for example in the form 1234 + day of the month.
Unsolved messages
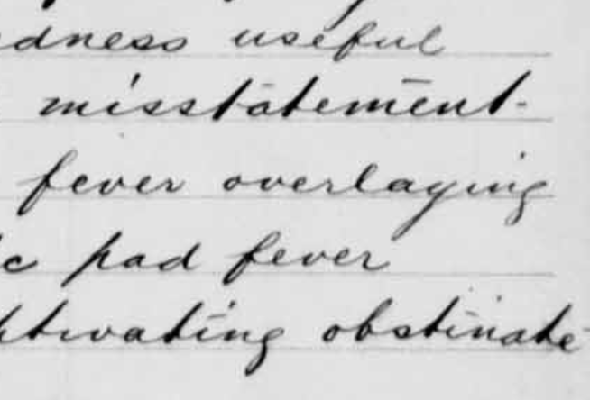
Unfortunately, Matthew could not solve all cryptograms yet, as you can see in his list. Of the unsolved messages, the following is particularly interesting:
Above some of the code words is a word written in shorthand. Can any reader decipher these notes? Of course, Matthew would also appreciate any other assistance. After all, there is still work to be done.
Finally, I would like to thank Matthew Brown very much for this great information! And of course I would like to congratulate him on the decryptions. It was not his first success: Matthew was also involved in cracking the letters of Charles I (together with Norbert Biermann and Thomas Bosbach).
Matthew is a computer game developer by profession and has been interested in cryptology for five years. At that time, Simon Singh’s book “Secret Messages” got him interested in the subject. I am pleased that he is now one of my blog readers.
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: Encryped telegram from 1948 deciphered
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/



Letzte Kommentare