Matthew Brown is the new bearer of the Friedman Ring
Matthew Brown has solved the challenge of Norbert Biermann. He is thus the new bearer of the Friedman ring.
The first person to solve the current crypto puzzle creates the next one. The Friedman Ring works according to this simple principle. This is a game named after cryptologists William and Elizebeth Friedman.
All previous winners can be found on this website.
Meanwhile the sixth round of the game is finished. The puzzle came from Norbert Biermann. Matthew Brown was the first to solve it. Shortly after him, Jarl Van Eycke also posted the correct solution. It was quite close.
Matthew Brown is thus the new bearer of the Friedman ring. Congratulations to all involved!
Norbert’s Challenge
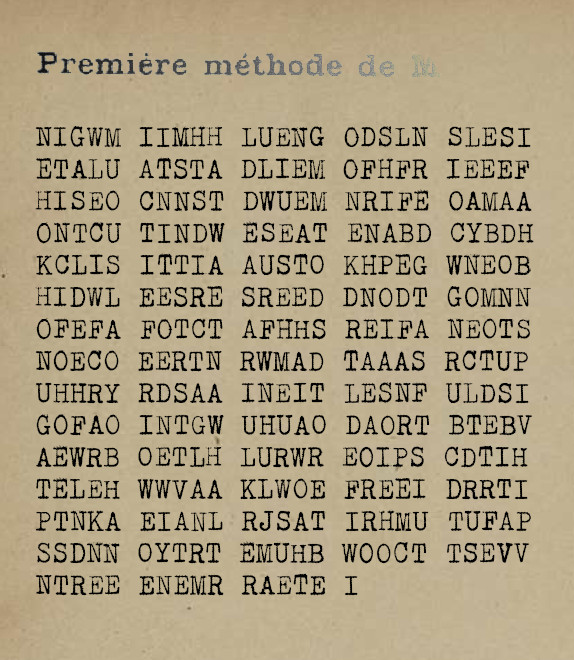
Norbert had created the following Challenge:
Norbert did not give any hints for this challenge. However, my readers rightly suspected that the headline gave a hint.
The process
Blog reader Rossignol was the first to guess that the method Norbert hinted at in the headline was Colonel Roche’s first method from Félix Delastelle’s book “Traité élémentaire de cryptographie” (1902). This is a transposition cipher, which is confirmed by the letter frequencies.
For the Roche method, one needs a multi-digit number as a key. In the said book, the number 52631574 is used, which I will adopt here. It is derived from 1/19=0.052631574…. derived.
First we have to prepare the key. This is done in several steps. Since the sum of the numbers in the key is 33, we can encrypt a text with 33 letters.
We write down the key as follows:
5|2|6|3|1|5|7|4
Then we replace each digit with a corresponding number of points:
.....|..|......|...|.|.....|.......|....
Now we write the numbers from 1 to 8 on the right position of each block:
....1|.2|.....3|..4|5|....6|......7|...8
Next, the numbers following 8 are written in the first free position after 1, 2, 3, and so on. Since there is only room for six numbers in this way, we accommodate the numbers 9-14:
....1|9 2|10 ....3|11.4|5|12...6|13.....7|14..8
Now we enter the numbers from 15 on in a similar way from the right (and thus come up to 20):
...20 1|9 2|10...19 3|11 18 4|5|12..17 6|13....16 7|14.15 8
Now again from the left:
...20 1|9 2|10 21 ..19 3|11 18 4|5|12 22.17 6|13 23 ...16 7|14.15 8
And so on:
..28 20 1|9 2|10 21 .27 19 3|11 18 4|5|12 22 26 17 6|13 23 ..25 16 7|14 24 15 8
And so on:
..28 20 1|9 2|10 21 29 27 19 3|11 18 4|5|12 22 26 17 6|13 23 30.25 16 7|14 24 15 8
And so on:
.32 28 20 1|9 2|10 21 29 27 19 3|11 18 4|5|12 22 26 17 6|13 23 30.25 16 7|14 24 15 8
In the end we get:
33 32 28 20 1|9 2|10 21 29 27 19 3|11 18 4|5|12 22 26 17 6|13 23 30.25 16 7|14 24 15 8
Now we have the prepared key. With it, we can encrypt as follows: If we assume a 33-letter plaintext, the 33rd letter comes first, then the 32nd letter, then the 28th letter, and so on.
As it turned out, Norbert had indeed used the Roche method.
The solution
But even if you know that a text was encrypted with the Roche method, the puzzle is not yet solved. You still have to find the key.
Mathew found that you don’t have to find the entire key at once, but can do it block by block, which allows a brute force attack. However, the scoring function Matthew used for each block did not necessarily produce the highest score for the correct solution, so Matthew always considered those 100 candidates with the highest score for the next round. In the end, he was successful. Almost at the same time, this was also true for Jarl, who used Hill Climbing for his attack.
Here is the key:
4,3,4,8,6,6,9,2,2,1,7,2,7,4,9,3,3,7,1,7,5,4,9,3,6,2,5,1,5,
9,2,7,4,5,4,7,1,6,6,2,6,3,5,9,1,5,7,9,7,1,7,2,2,7,8,2,1,9,
4,7,8,7,5,5,3,6,9,8,7,5,5,8
This sequence of numbers is derived from the square root of 18910924, which in turn stands for the birth date of cryptologist William Friedman. The plaintext is also about Friedman and his wife Elizebeth. It is based on a Wikipedia article:
William F. Friedman used his knowledge of rotor machines to develop several that were immune to his own attacks. The best of these was the SIGABA, which, after improvements by Frank Rowlett and Laurance Safford, would become the U.S.’s highest-security cipher machine during World War II. Just over ten thousand were built. A patent on SIGABA was filed in late nineteen forty-four but kept secret until two thousand and one, long after Friedman had died.
There are probably a few small errors in the plain text, but the key should be correct.
The next round is coming for sure
Matthew will now come up with a new puzzle for the next round. I am already curious. In about two months it will be: (Friedman-)Ring free for the next round!
At this point once again best thanks and congratulations to Matthew and Jarl as well as to Norbert, Joachim Rossignol, Doc Cool, Thomas Bosbach, Geoffrey Caveney, Jan, Nils Kopal, Chris, Gerd, David Vierra and Armin Krauß!
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: Ein kryptologischer Cold Case: Die BND-Challenges von 2014
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Letzte Kommentare