The Zschweigert challenge
In 1920, the German textile engineer Rudolf Zschweigert patented an encryption machine. Today I present a text that was encrypted with it. Can a reader solve it?
Last year I submitted a paper on Rudolf Zschweigert’s encryption machine for the HistoCrypt. This paper was accepted and then appeared in the conference proceedings, but the event itself was cancelled due to Corona. I was therefore unable to give the planned talk on the said machine.
Next Saturday (20 March 2021) I will have the opportunity to make up for the cancelled presentation, as a webinar at the International Conference on Cryptologic History (ICCH). This is already my seventh presentation in this series. This time it will take place at 5 pm (one hour earlier than usual) and is (as always) free of charge. The access data will be sent out via the mailing list, which you can subscribe to on the ICCH website. Anyone who does not want this subscription is welcome to send me an email and I will send him/her the link.
My partner for this talk is the British Jerry McCarthy, whom I have already reported on several times on Cipherbrain. Among other things, Jerry has rebuilt the Enigma-cracking machine “Zyklometer”.
The Zschweigert Cryptograph
The encryption machine developed by Zschweigert (Zschweigert cryptograph) is one of the many cipher machine designs created in the years after the First World War (1914-1918). Zschweigert was a textile engineer who had previously designed sewing and weaving machines, as evidenced by other patents, and apparently came up with the idea of building a cipher machine.
Unlike the Enigma and almost all other mechanical cryptographic devices, the Zschweigert cryptograph implements a transposition cipher and not a substitution cipher. Letters are not replaced here, but exchanged in the order.
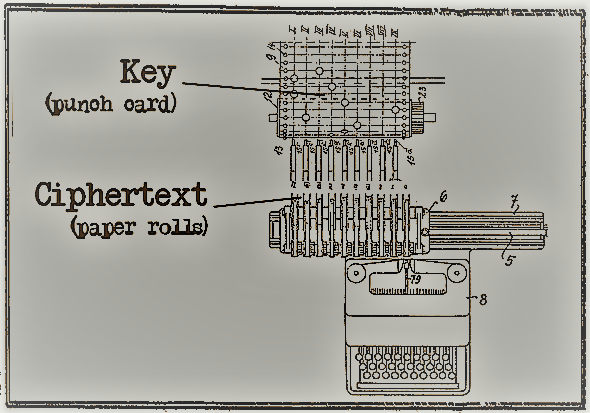
The Zschweigert machine worked with nine parallel paper rolls. The key was provided on a nine-column punched card. The number of rows of holes was arbitrary. There was exactly one hole per row. The machine worked through the plaintext letter by letter, jumping one row at a time on the punch card. The column in which the hole was located determined which roll was printed on. When the machine reached the last row, it jumped back to the beginning.
The following video shows how the machine worked (the punched card has five rows here):
If you want to know more, you can read my HistoCrypt work or the patent from 1920. This patent is the only source I know about the Zschweigert cryptograph. On the internet I found more information about Rudolf Zschweigert and his company, but the machine is not mentioned anywhere. While it is possible that it was built (as a prototype), I assume that it was never used in practice.
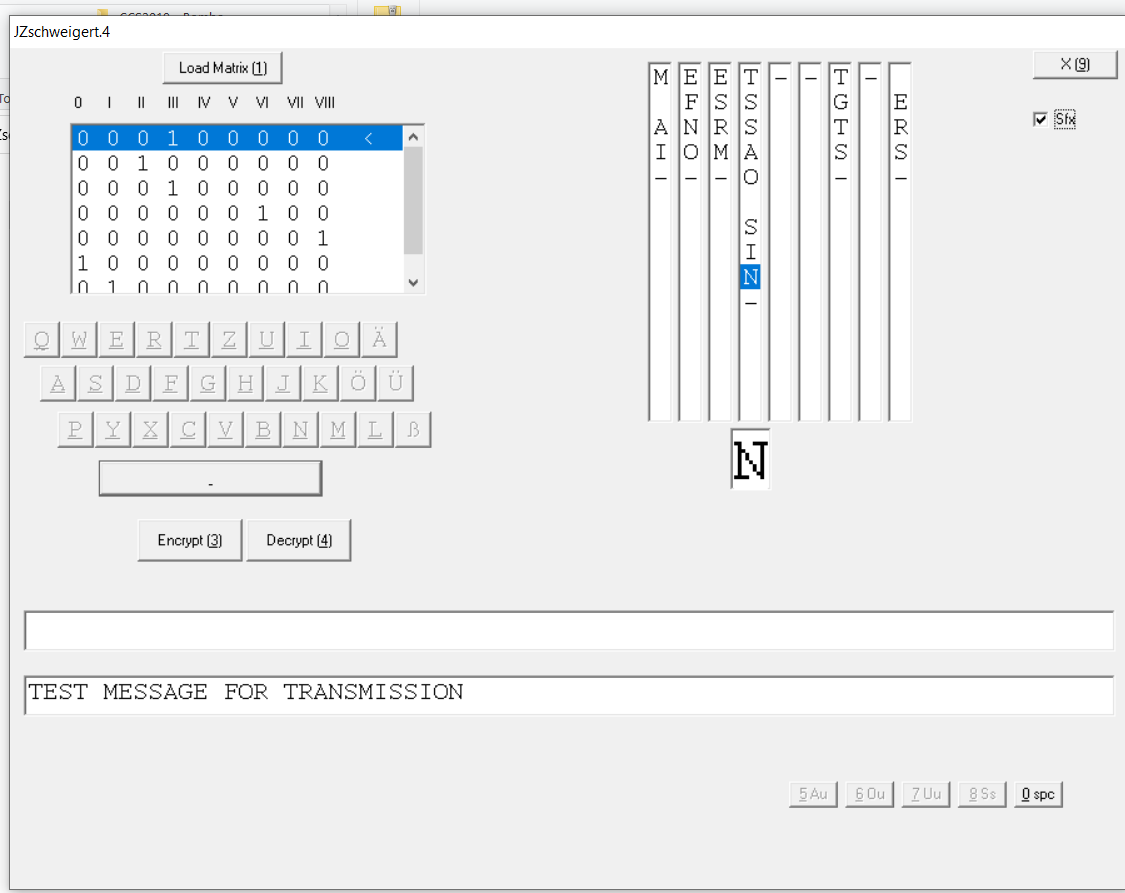
Jerry’s Zschweigert Simulation
The aforementioned Jerry McCarthy has programmed a computer simulation of the Zschweigert cryptograph based on my HistoCrypt work. Here is a screenshot:
In the lecture on Saturday, Jerry will present this software.
A Challenge
How secure the Zschweigert cryptograph is depends mainly on the key length. This is determined by the number of rows on the punch card. In the video, this card has only five rows, which is quite short. However, it should be possible to use much longer punch cards.
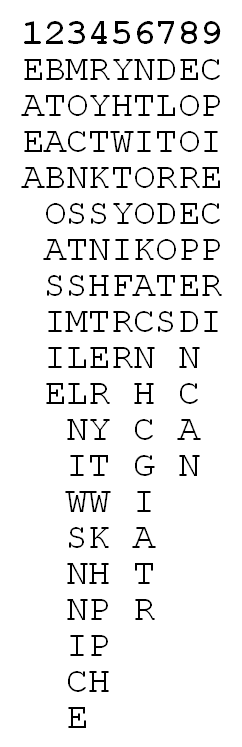
To find out a bit more about the security of this device, I created a challenge. For this purpose, I encrypted an English text with just over 100 letters using the Zschweigert cryptograph method. The result looks like this:
Read out column by column, you get the following ciphertext:
EAEA-BTABOASIIE-MOCNSTSMLLNIWSNNICE-RYTKSNHTERYTTWKHPPH-YHWTYIFRR-NTIOOKACNHCGIATR-DLTRDOTS-EOOREPEDNCAN-CPIECPRI
The number of rows on the punch card is part of the key.
Can a reader crack this cryptogram? If someone succeeds by next Saturday, I will of course mention this in the lecture.
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: Prince Edward opens new exhibition at Bletchley Park
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/




Letzte Kommentare