In the Second World War, the Germans constructed a voice encryption machine. I have only very little information about this device. Can my readers help me to find out more?
In five weeks, at the Charlotte International Cryptologic Symposium, I will give a presentation about German ciphers in World War II. Of course, I will mention the Enigma, but my focus will lie on the less known German encryption systems. There are pretty many. I am aware of about a dozen machines, a dozen codebooks, over 20 manual ciphers, five encryption devices, and several steganographic methods the Germans used during WW2. I’m sure my list is not complete.
German encryption machines
The German encryption machines I will cover in my talk are mainly the ones mentioned in my blog post from 2016.
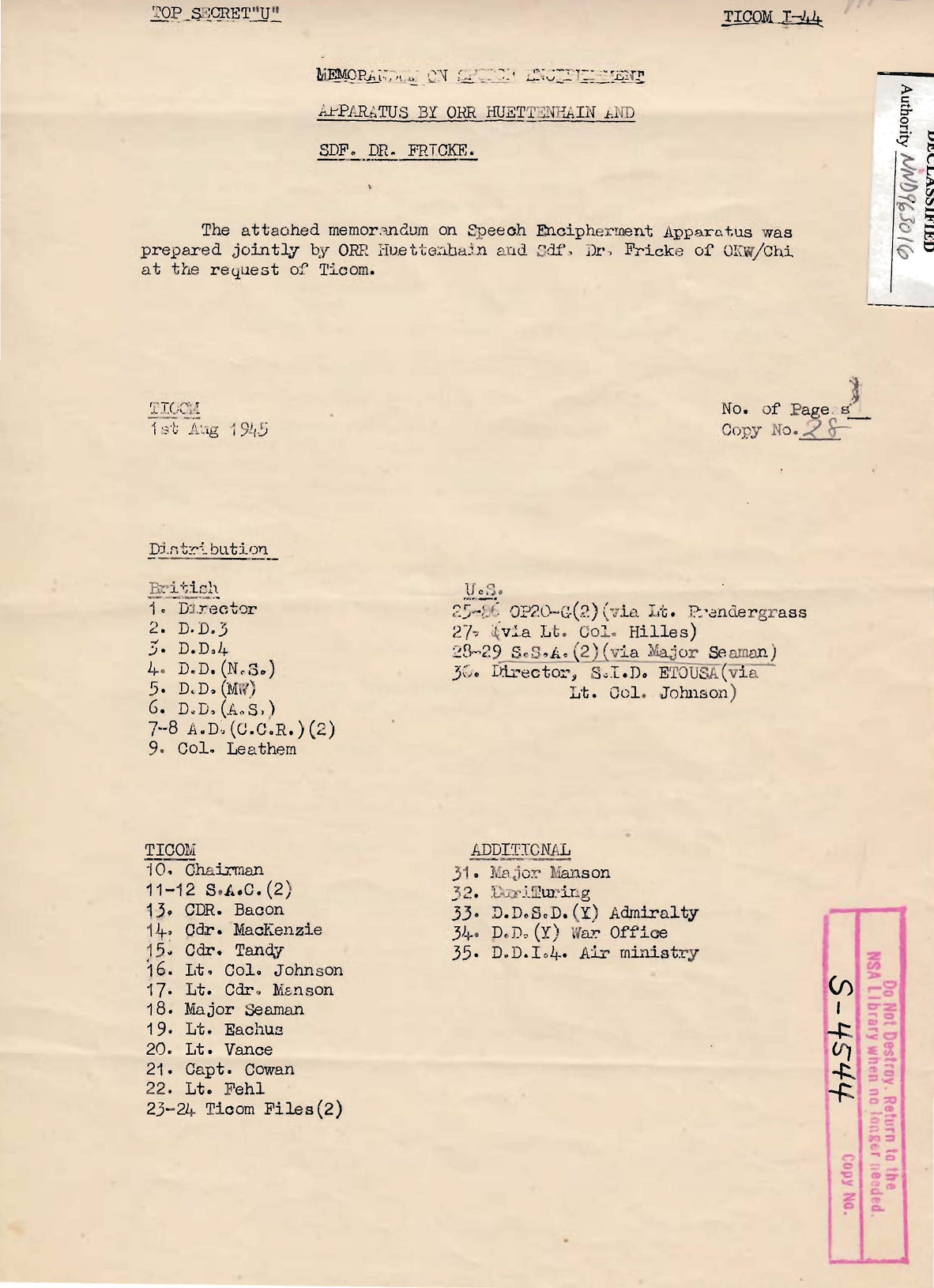
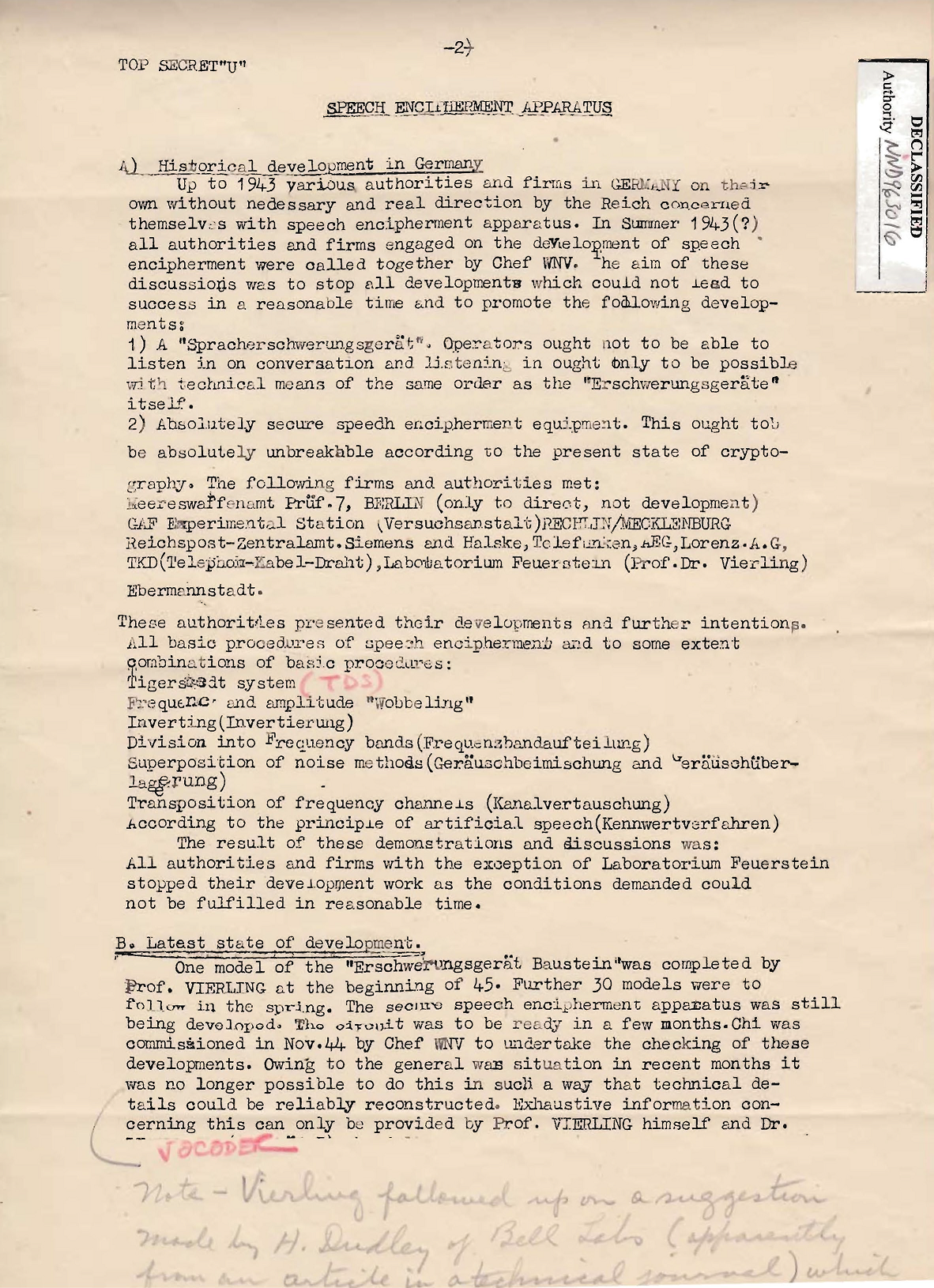
In this post, I mentioned that a journalist once had told me that the German WW2 general Erwin Rommel used a voice encryption machine in the tanks of the Africa corps. This sounded very interesting, but in the literature I was aware of this device was not mentioned. In a comment, blog reader Thomas Bosbach provided me a link to a TICOM document that mentions a speech encipherment apparatus. This device might be identical with the Rommel voice encryptor.
Voice encryption
Technically speaking, voice encryption is completely different from encrypting a text (most of the methods covered on this blog encrypt text). In WW2, voice encryption was still in its infancy. The Americans constructed a voice encryption machine named SIGSALY, which was as good as unbreakable, but extremely large and expensive. Only a few copies were built.
In the UK, Alan Turing built a voice encryption machine named DELILAH.
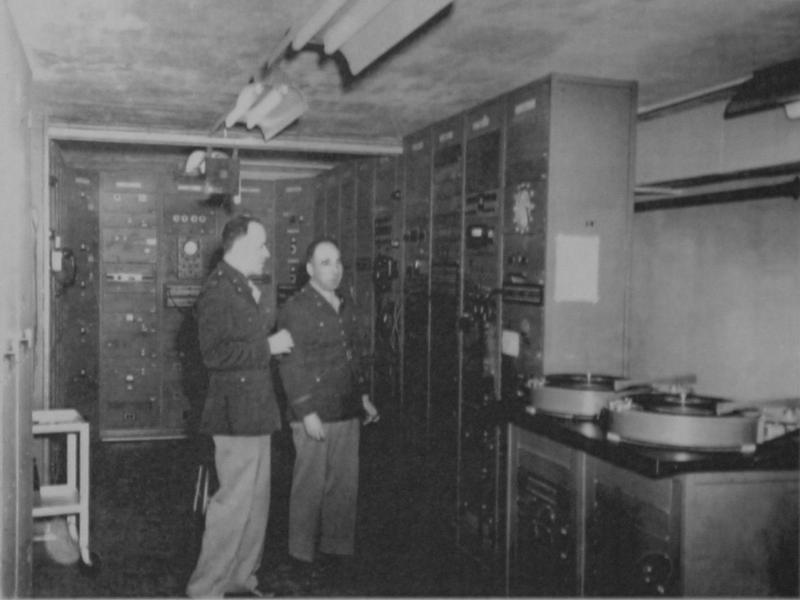
DELILAH was never used in practice. There was also a Russian voice encryption device. I have never seen a picture of it. The Germans constructed a device that automatically broke this Russian voice encryption. Here’s a photo of it (provided by Klaus Kopacz):
All in all, voice encryption didn’t play much of a role in WW2. The technology was still to immature to be really useful. For more information, I recommend the book How to Wreck a Nice Beach by Dave Tompkins (yes, the book is as good as its title).
The speech encipherment apparatus
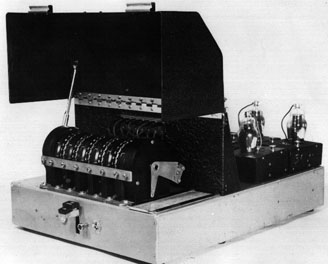
The afore-mentioned TICOM document not only describes a speech encipherment apparatus, but also a so-called “Erschwerungsgerät” (aggravating device). This machine encrypted voice transmissions in a simple way. It was easy to break, but at least it prevented listening to a transmission with an ordinary radio device.
Here’s page 1 of the document:
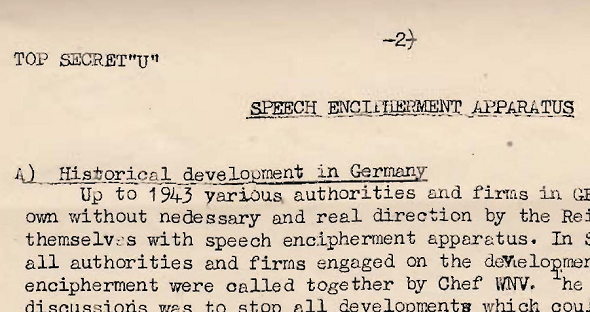
The second page mentions that several companies and authorities in Germany worked on voice encryption devices during WW2. In 1943, the Wehrmacht tried to combine forces.
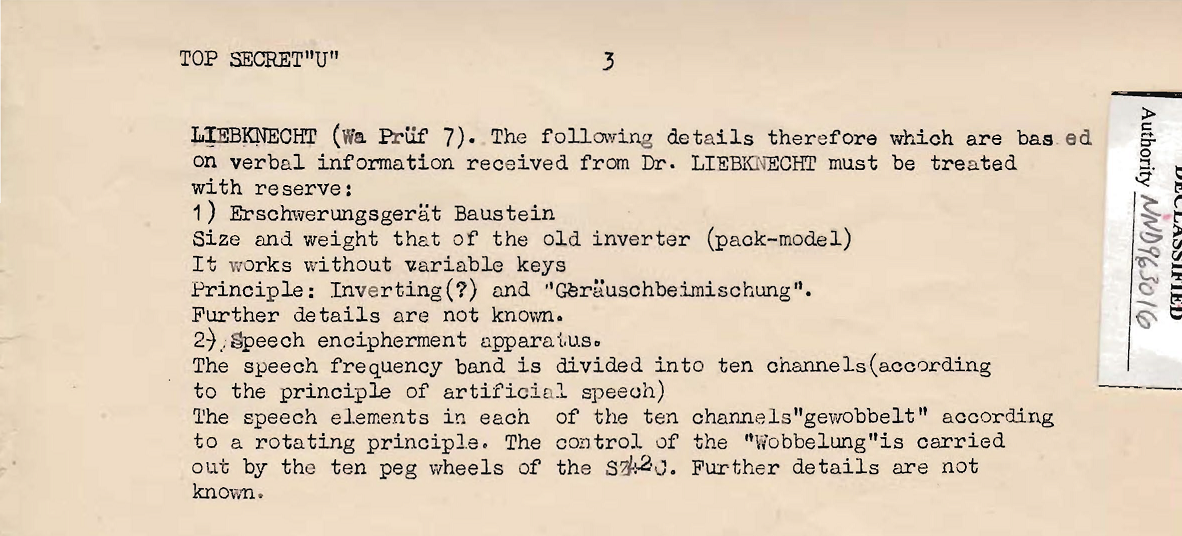
The third page contains a very brief description of the speech encipherment apparatus:
This document is the only one I know that covers German voice encryption technology in WW2. I have never seen a picture of a German WW2 speech encipherment apparatus, let alone a machine itself.
Does a reader know more about this topic? Any information is welcome.
Follow @KlausSchmeh
Further reading: A fascinating report of Enigma’s contemporary witness, Max Rüegger
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/




Kommentare (13)