Only little is publicly known about the encryption systems used by the German terrorist organisation, RAF. A recent TV documentary that shows a number of encrypted RAF messages along with a key provides at least some basic information.
The Red Army Fraction (RAF), a West German terrorist organisation, existed from 1970 to 1999. The RAF engaged in a series of bombings, assassinations, kidnappings, bank robberies, and shoot-outs with police. Their activity peaked in late 1977, which led to a national crisis that became known as the “German Autumn”. The RAF is held responsible for 34 deaths throughout its almost three decades of activity.
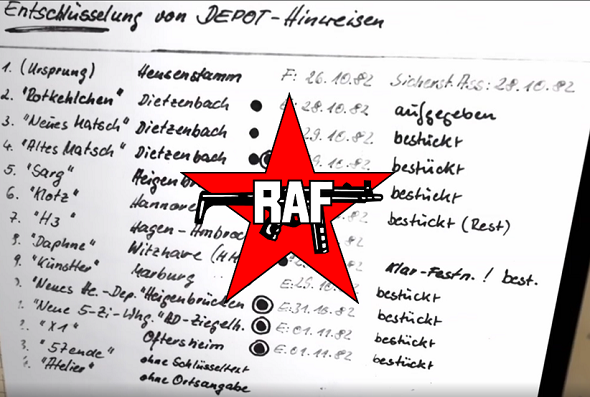
It has long been known that the RAF used cryptography and that the police was able to break some of the RAF ciphers. This was especially important when in 1982 an RAF depot containing weapons, identity documents and money was detected in a forest near Heusenstamm in the Frankfurt area.
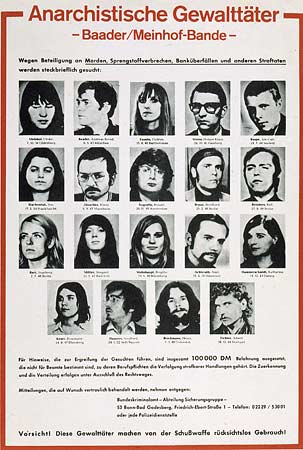
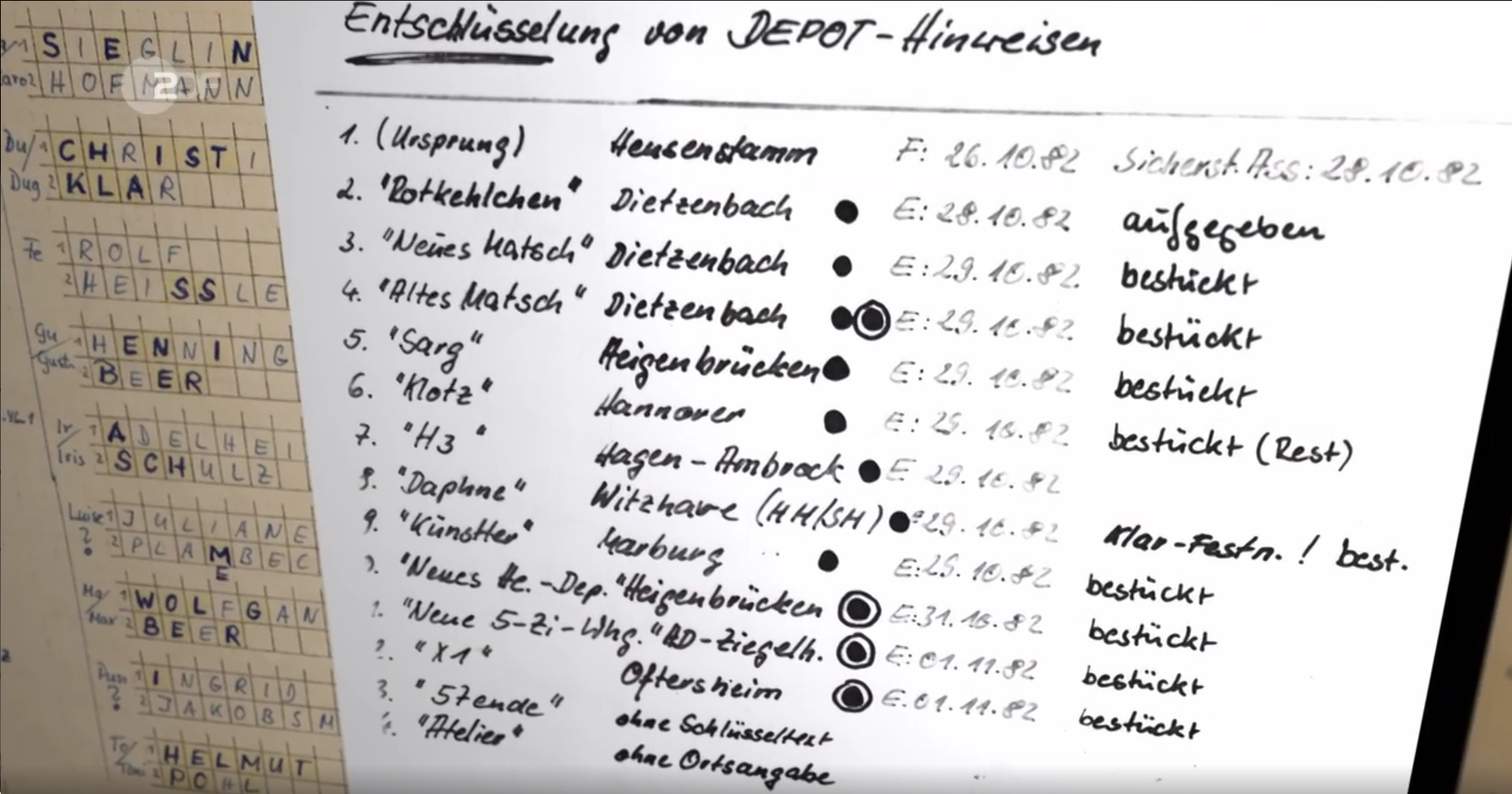
In the Heusenstamm depot, police found a number of encrypted documents. When police cryptanalysts broke these messages, the location of several other depots became known. All depots were put under 24 hour surveillance. Two weeks later, RAF terrorists Brigitte Mohnhaupt and Adelheid Schulz were arrested when they visited the Heusenstamm depot.
After the arrest of the two top terrorists, the existence of the Heusenstamm depot was mentioned in the press and thus became publicly known. Christian Klar, the most important RAF terrorist of the time, apparently believed that the encryption code was still unbroken and therefore assumed that the police did not know about the other depots.
When Klar, disguised as a jogger, approached an RAF depot located in Hamburg, police guards arrested him.
Of course, crypto history enthusiasts would have liked to know how the RAF encryption codes worked, but to my knowledge as good as nothing has ever been published. Blog reader Steffen (DG0MG) has now made me aware of a German TV documentary about the RAF (28:29) that contains some very interesting information.
According to this TV documentary, a German forensic codebreaker named Peter Fleischmann played an important role in breaking the ciphertexts found in Heusenstamm. I have never heard of this man before, and I can’t find anything about him online. He would certainly be a great interview partner for me (he’s apparently still alive). So, if a reader knows how I can get in touch with Peter Fleischmann, please let me know.
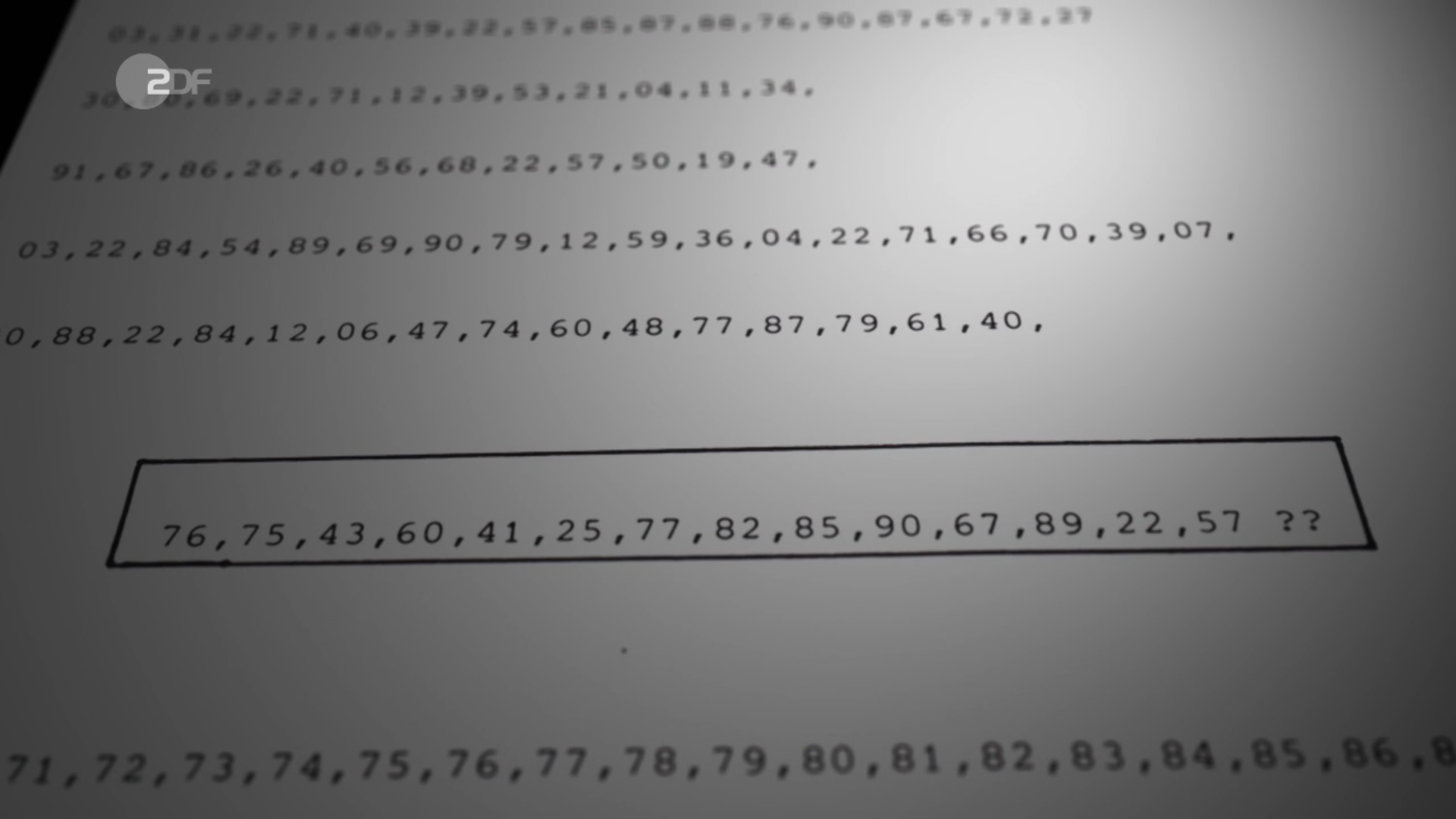
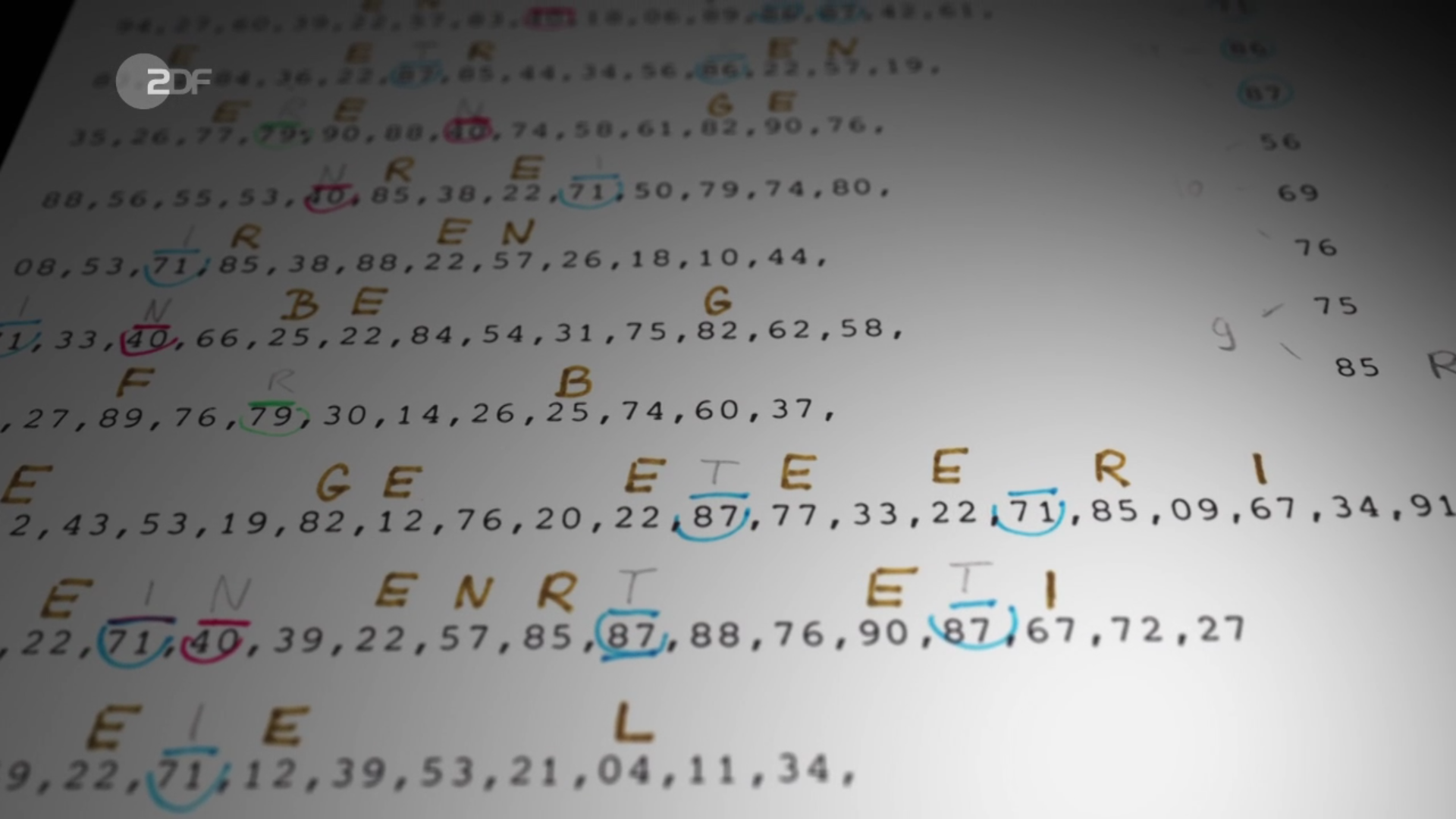
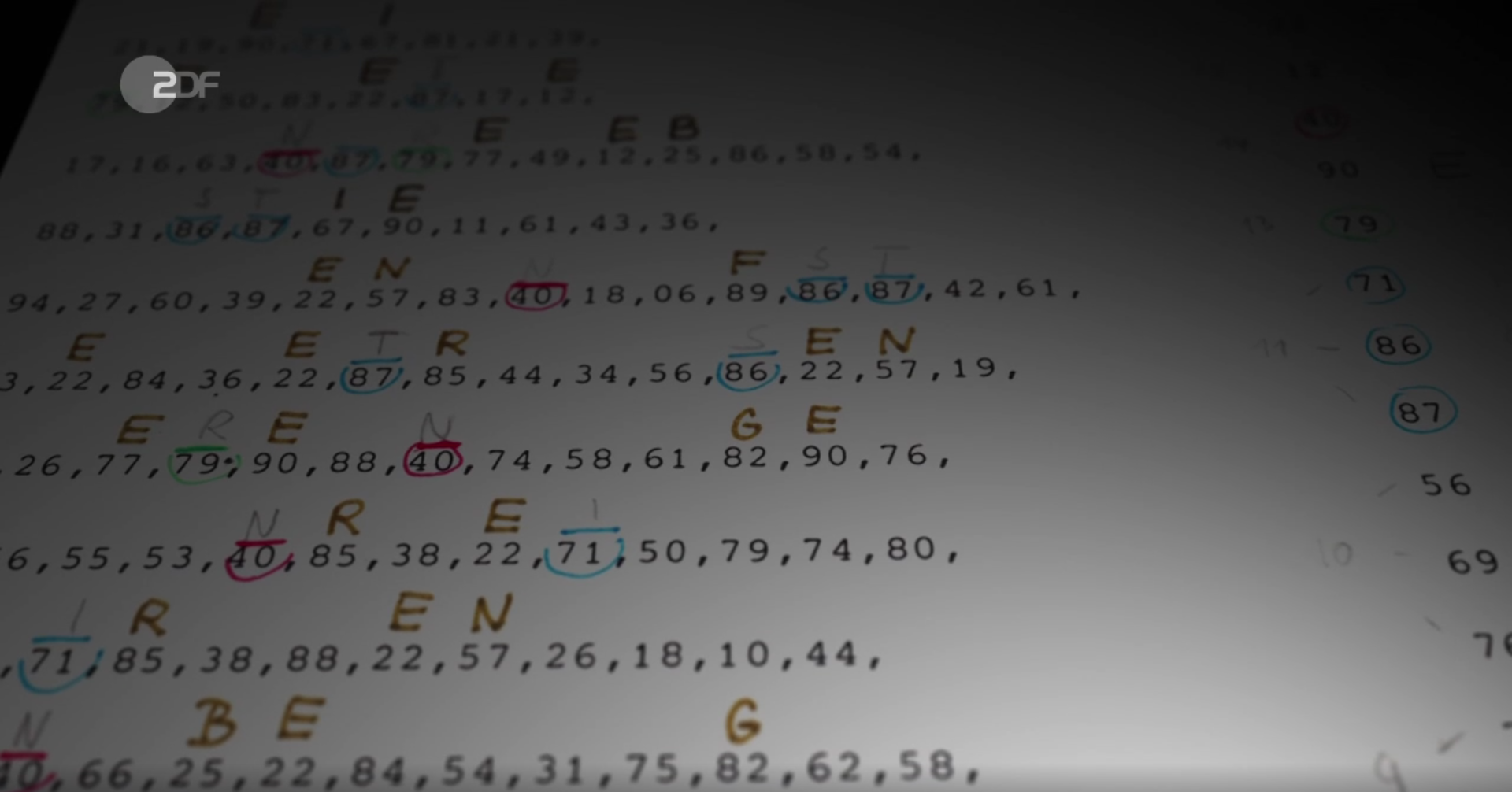
Apparently, one of the ciphers used by the RAF was a substitution cipher. The following screenshots show messages encrypted in this system:
In the documentary, Peter Fleischmann explains that he and his colleagues solved this cipher using a crib. When they encountered a ciphertext word of the type ABBC, which apparently stood for a gas station, it was clear that this could only be ESSO (the brand name used by the US company Exxon in Germany and many other countries). Having identified the letters E, S, and O, the cipher could be broken.
The following document is probably a code that provides codewords for a number of words:
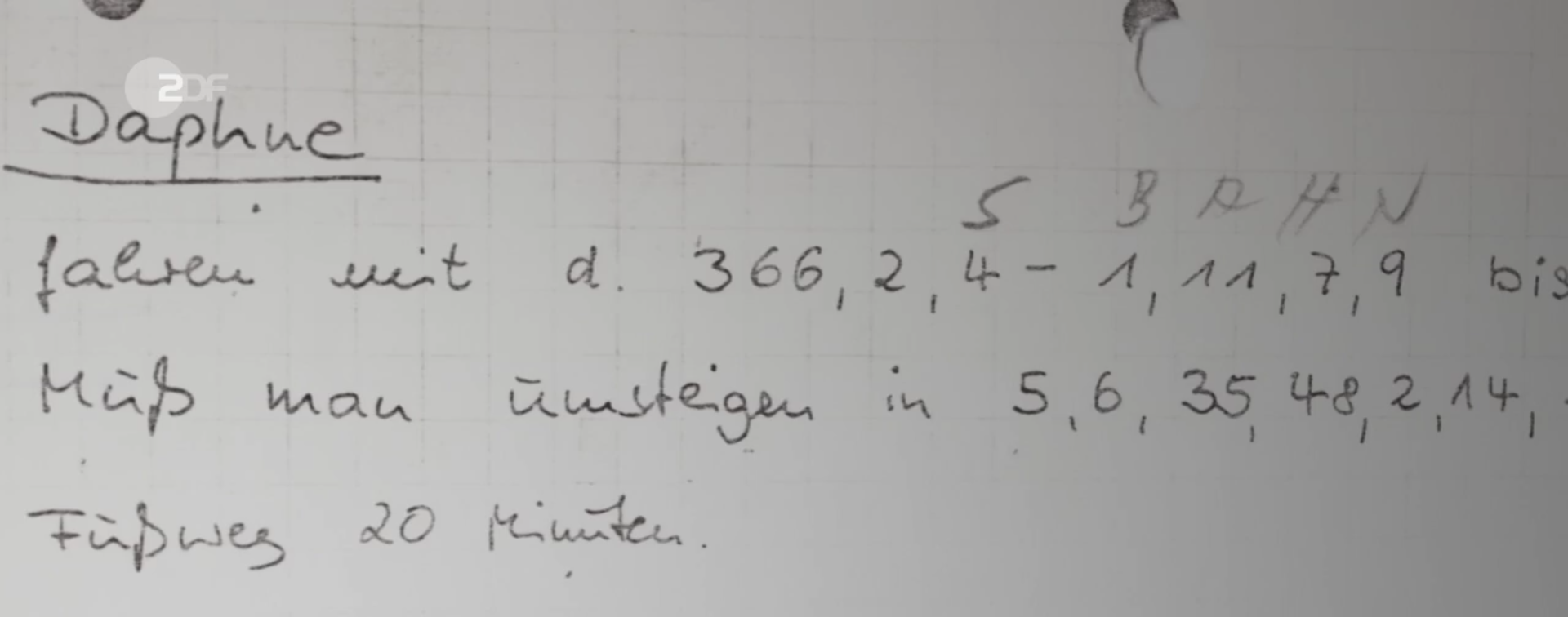
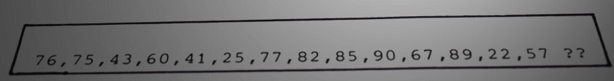
Of course, I would like to know more about the codes the RAF used. If you have some information or if you can make sense of the messages depicted in this article, please let me know. For instance, it would be interesting to know what the following passage means:
Any help is welcome.
Follow @KlausSchmeh
Further reading: The Top 50 unsolved encrypted messages: 24. The Erba murder cryptogram
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (11)