Five years ago an encrypted carrier pigeon message from World War II hit the news. So far, nobody has been able to decipher it.
Click here for the complete top 50 list
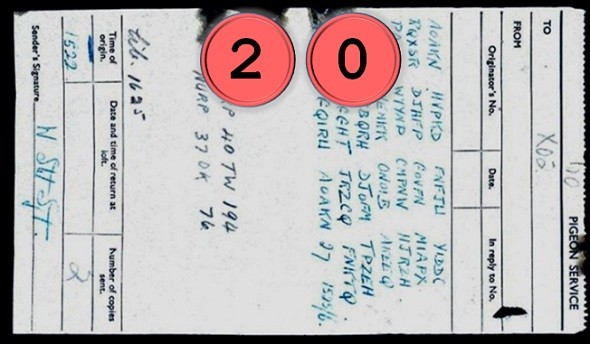
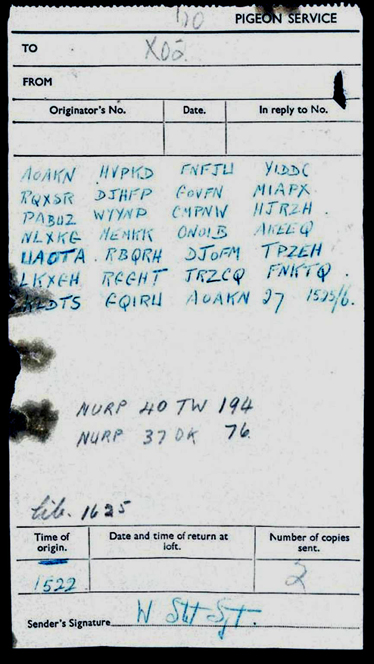
In August 2012, David Martin from Surrey, UK, made an interesting find. In the chimney of his house he discovered the skeleton of a carrier pigeon along with a message still wrapped to its leg. As it turned out, the message was encrypted:
The message is not dated. However, the pigeon wore a ring indicating that it was born in 1940. According to historians, the message was probably sent from France to England on D-Day (June 6th, 1944) by a Sergeant W. Stott. It seems possible that the pigeon was heading for Bletchley Park, where the British operated their crypto and codebreaking institution. Bletchley Park lies about 130 kilometers to the north of the finding place.
The pigeon cryptogram
The use of carrier pigeons was quite common in World War II. The British air force trained about 250,000 birds, forming the National Pigeon Service. Typically, the pigeons were dropped into Nazi occupied Europe using parachutes. Agents picked them up and provided them to the British military for sending messages back home.
As good as nothing is known about the ciphers the British used for encrypting their carrier pigeon traffic. The message found in Surrey is the only encrypted carrier pigeon message from WW2 I have ever heard of. It is therefore pretty hard to say what kind of encryption was used. Crypto history experts at Bletchley Park (which is now a museum) and the British secret service GCHQ tried to decipher it, but to no avail.
Meanwhile many others have tried to break the pigeon encryption. At least two persons claimed to have solved the mystery, but none of these solutions has been accepted by crypto experts.
The carrier pigeon cryptogram is covered in a German blog post I wrote in 2013.
Hard to break
Here’s a transcription of the pigeon message:
AOAKN HVPKD FNFJW YIDDC
RQXSR DJHFP GOVFN MIAPX
PABUZ WYYNP CMPNW HJRZH
NLXKG MEMKK ONOIB AKEEQ
UAOTA RBQRH DJOFM TPZEH
LKXGH RGGHT JRZCQ FNKTQ
KLDTS GQIRW AOAKN 27 1525/6.
The message contains 27 groups of five letters each. The group AOAKN appears twice – at the start and at the end. It might therefore be a call sign or something similar.
Here are a few hypotheses that have been discussed:
- The message might have been encrypted with a manual cipher. To my regret, there seems to be no systematic overview on British manual ciphersused in WW2. A bigram substitution seems to be an interesting candidate.
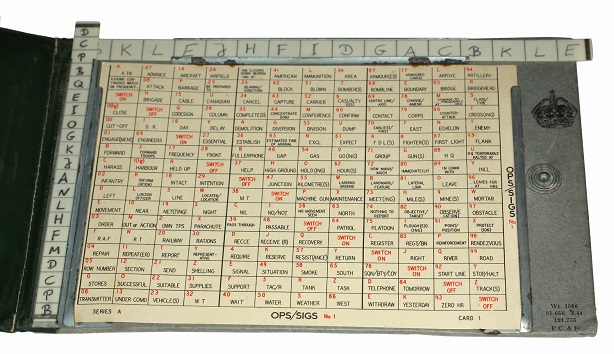
- A Slidex (a British WW2 lowtec encryption device) might have been used. However, this hypothesis was rejected by Nick Pelling.
- The message might have been encrypted with the British encryption machine Typex (the Typex ressembles the German Enigma but is more advanced):
- The message might have been encrypted with a codebook. If so, the only way to solve the message is finding the codebook that was used (the one shown below is certainly not the correct one). Even worse, in addition to the codebook, a second encryption step might have been applied – a quite common procedure.
The carrier pigeon cryptogram received a lot of media coverage. There’s no doubt that many skilled people tried to break it. We can therefore assume that the carrier pigeon cryptogram is extremely hard to decipher. Maybe one of my readers will be successful anyway.
Follow @KlausSchmeh
Further reading: The Top 50 unsolved encrypted messages: 27. Ferdinand III’s encrypted letters
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/




Kommentare (6)