A recent book mentions a cipher used by a German spy during the Second World War. Can you break a message I encrypted with this method?
George Lasry, …

… a world-class codebreaker from Israel and reader of this blog, has made me aware of a book published in 2018: Codebreaker: The untold story of Richard Hayes by Marc McMenamin. This book is about Richard Hayes, a gifted polymath and cryptographer from Ireland, who was drafted by Irish intelligence services to track the movements of German spy Hermann Görtz.
Source: National Library of Ireland
The cipher
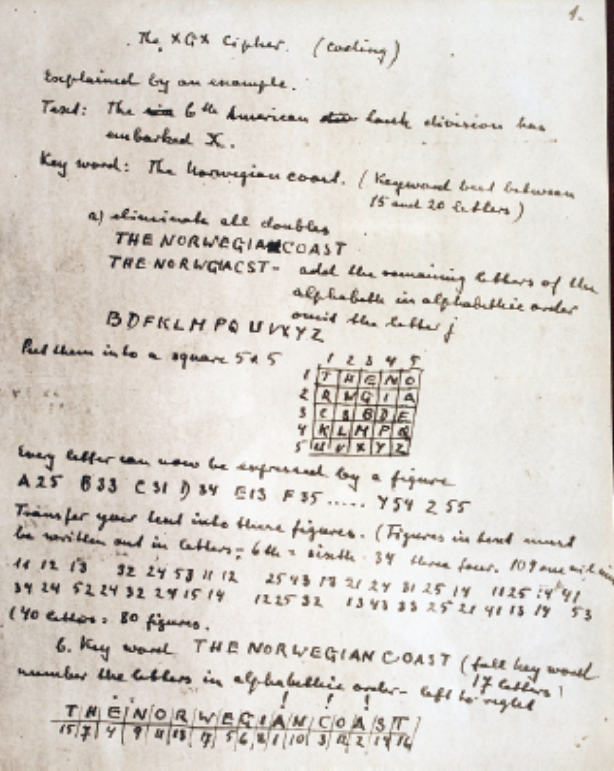
The book contains a scan of the original cipher description Görtz used. The cipher is explained with the following plaintext:
THE SIXTH AMERICAN TANK DIVISION HAS UNBARKED X
The cipher requires a key word or key phrase. The description uses a phrase: THE NORWEGIAN COAST
In the first step, the key phrase is used to construct a 5×5 matrix (write the key phrase line-wise; if the same letter appears twice, omit the second one; fill the rest of the matrix with the remaining letters of the alphabet; the letter J is ommitted because it is identified with I).
THENO RWGIA CSBDF KLMPQ UVXYZ
Based on this matrix we construct a substitution table. It looks like this:
11=T, 12=H, 13=E, …
21=R, 22=W, …
…
With this substitution we encode the plaintext:
11 12 13 32 24 53 11 12 25 43 13 21 24 31 25 14 11 25 14 41 34 24 52 24 32 24 15 14 12 25 32 13 43 33 25 21 41 13 14 53
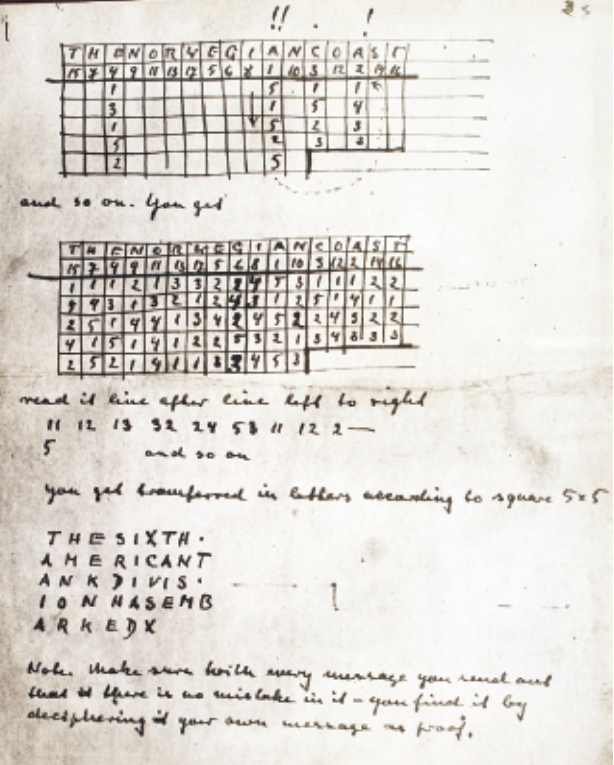
Next, we perform a columnar transposition. For this purpose we use the same password again (it would certainly be better to apply a new one now, but apparently the German cryptologists thought it was too complicated for a spy to remember two words or phrases). To prepare the transposition, we write the encoded message (11 12 13 32 …) row-wise below the passphrase:
THENORWEGIANCOAST 11121332245311122 54313212431251411 25144134245224322 41514122532134333 252141131453
Now we sort the table such that the top row is ordered alphabetically:
AACEEGHINNOORSTTW 51112214231132123 14532443123121511 53214254424412223 23352513114413432 5 23154134 1 2 1
In the last step we read out the ciphertext column-wise:
51525 1433 1523 13152 22423 24151 14515 43434 21411 32213 13444 1144 32111 2123 15242 2123 31321
Usually, the ciphertext is written in groups of five:
51525 14331 52313 15222 42324 15114 51543 43421 41132 21313 44411 44321 11212 31524 22123 31321
Source: National Library of Ireland
The challenge
There are about a dozen German spy ciphers from World War 2 I am aware of (at the HistoCrypt 2017 I gave a presentation about German WW2 spy ciphers). This one is certainly one of the best (remember that a spy cipher had to be simple and that using a cipher tool, let alone an encryption machine, was prohibitive). Anyway, it is clear that this method is not unbreakable. To test the security of Görtz’s cipher, I have created a challenge. The following message is encrypted in exactly the way described above, but with a different key word or phrase:
11331 42451 31211 33233 11144 42433 55112 13455 24342 43342 32341 51242 12425 32511 42353 11554 53213 23512 43233 31521
Can you decipher this message?
Follow @KlausSchmeh
Further reading: The Top 50 unsolved encrypted messages: 45. The World Record Challenge
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (30)