CB FT MH GR IO TS TA UF SB DN WG NI SB RV EF BQ TA BQ RP EF BK SD GM NR PS RF BS UT TD MF EM AB IM
How to break a Playfair encryption
Using a computer, there are two ways to attack a Playfair cipher:
- Dictionary attack: If a keyword has been used for creating the matrix, it is possible to break a Playfair cipher by key word guessing. For instance, the word SURPRISE is contained in virtually every English dictionary, so a computer that tests one keyword candidate after the other will sooner or later find it.
- Hill Climbing: Hill Climbing is the current super-algorithm of historical codebreaking. As Nils Kopal and George Lasry have shown, Hill Climbing (enhanced with Simmulated Annealing) can break a Playfair cryptogram of 40 letters.
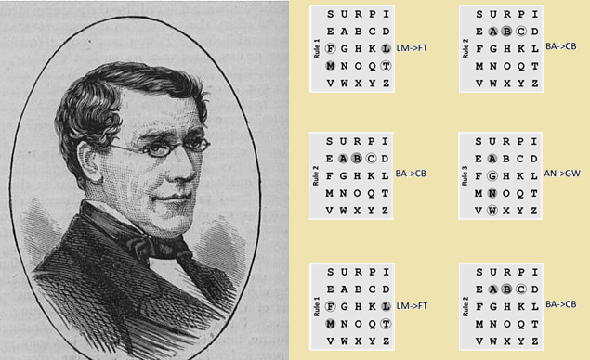
There are several books that explain how a Playfair can be broken without computer support – for instance Helen Fouché Gaines’ Cryptanalysis, André Langie’s Cryptography, and William Friedman’s Military Cryptanalysis. The concept is to guess a few words in the plaintext and to derive the 5×5 matrix based on the peculiarities of the Playfair cipher (for instance, if AB->XY then BA->YX).
However, breaking a Playfair cryptogram this way is pretty difficult, especially if the ciphertext is short. To make things not too complicated, the books mentioned above use messages containing several hundred letters for demonstration. In addition, these books assume that a few words of the plaintext are known or can be guessed. None of these books describes the complete Playfair codebreaking procedure, as this would require too much space – instead, they simply omit most of the trial-and-error reckoning involved in breaking a Playfair cryptogram.
A new Playfair challenge
After my Playfair cryptogram consisting of 40 letters was solved, it made sense to create an even shorter one. I decided to take a 30-letters cleartext. Here is my new challenge:
SXCREDBQUGVZRSMNDSIKRKWRSGNSNXVM
The ciphertext has exactly 30 letters (spaces not included). The plaintext is in English. I used the software CrypTool 2 for encryption. As far as I know, CrypTool implements the Playfair cipher exactly the way it is explained above. The keyword is a random transposition of the alphabet. No keyword is used. So, a dictionary attack won’t work.
As mentioned, solving this challenge will set a new record. Good luck!
Follow @KlausSchmeh
Further reading: A mird in the hand is worth two in the mush: Solving ciphers with Hill Climbing
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (9)