CrypTool is the world’s leading crypto e-learning software. Currently, the 20th anniversary of this outstanding tool is celebrated in Munich. Among the guests are some renowned codebreakers.
In my blog posts, I often mention the open-source software CrypTool. When it comes to performing codebreaking tasks, such as frequency analysis or computing the index of coincidence, CrypTool is extremely helpful. However, CrypTool can do much more. It supports hundreds of crypto functions, including AES, RSA, Diffie-Hellman, MASCs, ADFGVX, turning grilles, and transpositions. Many of these methods are visualized, which helps the user to understand what is going on. All in all, CrypTool is a great crypto e-learning and codebreaking software.
20 years, over 400 crypto functions
The CrypTool project started in 1998 at Deutsche Bank. The concept was developed by Bernhard Esslinger, who is today a professor at the University of Siegen. Over the years, this software grew to a more and more powerful tool. Numerous companies (such as my employer cryptovision) and non-commercial organisations provided code for CrypTool. Students developed CrypTool functionality as part of their theses.
Meanwhile, there are four CrypTool variants: CrypTool 1, CrypTool 2 (the one I usually work with), JavaCrypTool and CrypTool-Online. More than 400 crypto-related functions are implemented in these four programs.
Starting this morning, the CrypTool team is currently celebrating the 20th anniversary (yes, meanwhile it is one year too late) of their project in Munich, Germany.

Source: Schmeh
I have the honor of taking part in this event. My main contribution to the CrypTool project is that I have mentioned this software in many of my books, articles, research works and blog posts. I hope that my work has helped a little to make CrypTool more popular.
The following picture shows the five fathers of CrypTool (Prof. Arno Wacker, Jörg Schneider, Dominik Schadow, Henrik Koy, Prof. Bernhard Esslinger):

Source: Schmeh
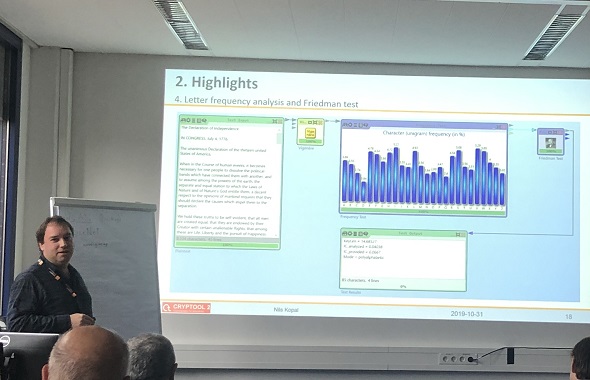
Today, the main developer of CrypTool 2 is Nils Kopal. The next picture shows him demonstrating the software:

Source: Schmeh
MTC3
Another part of the CrypTool project, managed by almost the same people, is the MysteryTwister C3 (MTC3) website. MTC3 is the most popular crypto challenge portal worldwide. It provides hundreds of ciphertexts for the user to break, in four different difficulty levels (some of these challenges were provided by me). For solving a challenge, a user gets a certain amount of points. The most successful solvers are displayed in a hall of fame.
At the CrypTool anniversary celebration, four of the five most successful MTC3 participants are present. Here they are:

Source: Schmeh
Hajo Eilau (#2), Kurt Gebauer (#5), George Lasry (#1), and Armin Krauß (#4). All four are world-class codebreakers. Readers of this blog might know George and Armin, who have been mentioned many times on this blog. Hajo and Kurt are newcomers in the codebreaking scene. I have never met them before. I hope we will hear a lot from them in the future.
Follow @KlausSchmeh
Further reading: The Top 50 unsolved encrypted messages: 8. The Catokwacopa cryptograms
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (6)