A children’s book from the 1980s contains numerous encrypted and hidden messages. Can a reader solve four of these?
Are you looking for a nice Christmas present? If so, consider my crypto history books. Provided that the recipient can read German, Nicht zu knacken, Codeknacker gegen Codemacher, and Versteckte Botschaften are certainly a good choice.
—————————————–

I’m excited to announce I’ll be speaking at RSAConference 2020 on UNDERSTANDING AND EXPLAINING POST-QUANTUM CRYPTO WITH CARTOONS.
—————————————–
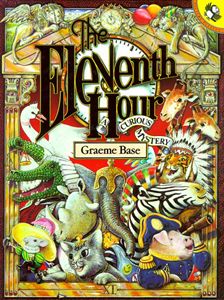
The Eleventh Hour
If you are looking for a present for an English-speaking person and if this person is still a child, The Eleventh Hour by Graeme Base is worth considering.
Source: “The Eleventh Hour”
Here’s what Wikipedia writes about The Eleventh Hour:
In it [The Eleventh Hour], Horace the Elephant holds a party for his eleventh birthday, to which he invites his ten best friends (various animals) to play eleven games and share in a feast that he has prepared. However, at the time they are to eat—11:00—they are startled to find that someone has already eaten all the food. They accuse each other until, finally, they’re left puzzled as to who could have eaten it all. It is left up to the reader to solve the mystery, through careful analysis of the pictures on each page and the words in the story.
Source: “The Eleventh Hour”
Written in rhyme, the book includes large and lavish full-page illustrations of Horace’s opulent house and the events of the party, packed with hidden details. The author invites the reader to deduce the identity of the thief by examining the illustrations and making deductions and observations.
What makes The Eleventh Hour interesting for this blog is that in the illustrations messages are hidden. For instance, the frame of one page consists of Morse code while another page includes a message encoded in musical notes. Several pictures contain number or letter sequences that have a meaning. On a chess board, pigpen letters can be seen, while characters written on tennis balls spell out another message. It’s almost impossible to find all the messages hidden somewhere in the drawings.
A paragraph of ciphertext at the end of the book delivers the solution of the “criminal case” the book is about. It is encrypted in a Caesar cipher and therefore pretty easy to solve. The plaintext offers an additional challenge to the reader.
In the last section of the book, all solutions are given.
Four challenges
In the following, I will provide four crypto challenges that are contained in The Eleventh Hour. All of them have been encrypted in the same way.
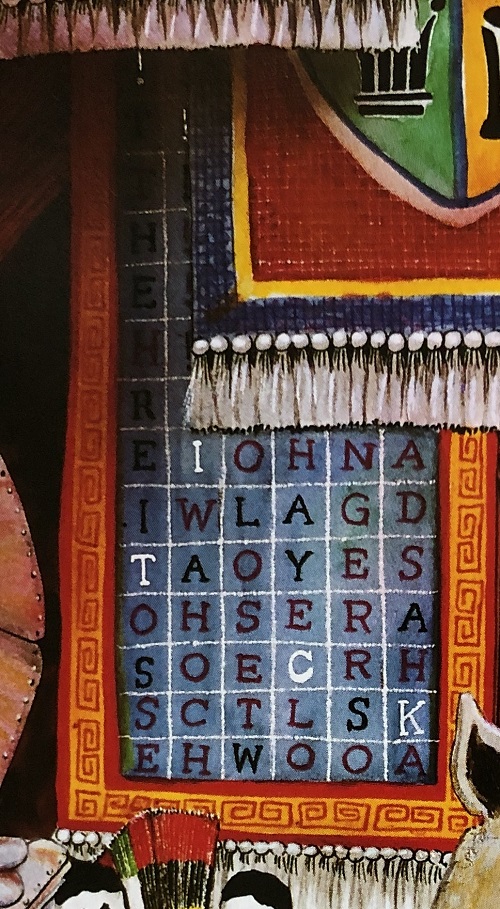
#1
Source: “The Eleventh Hour”
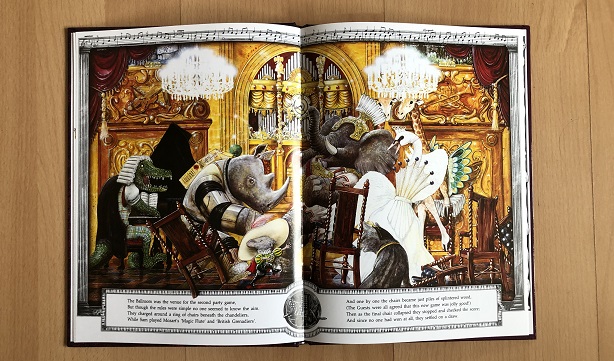
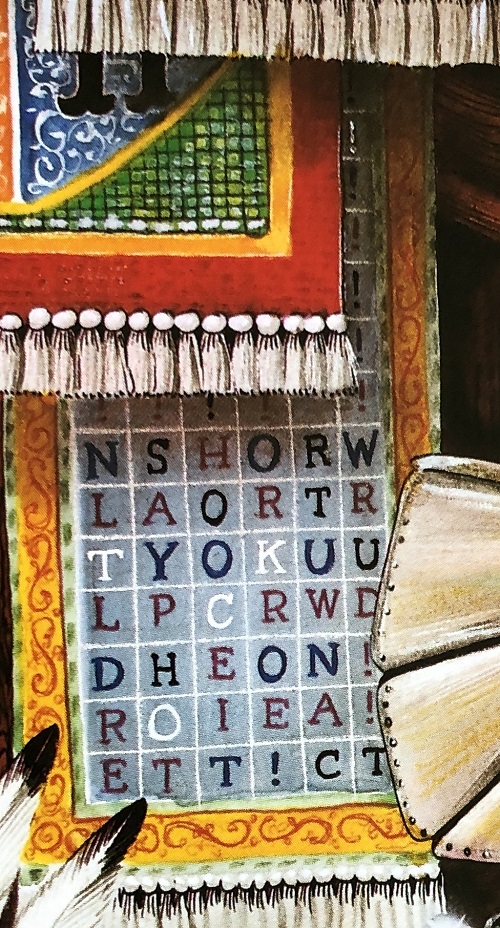
#2
Source: “The Eleventh Hour”
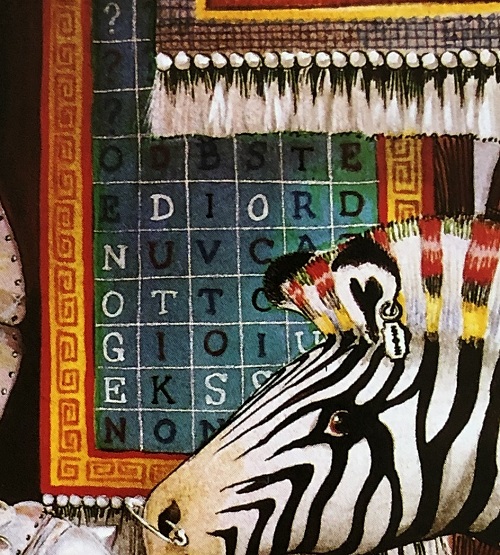
#3
Source: “The Eleventh Hour”
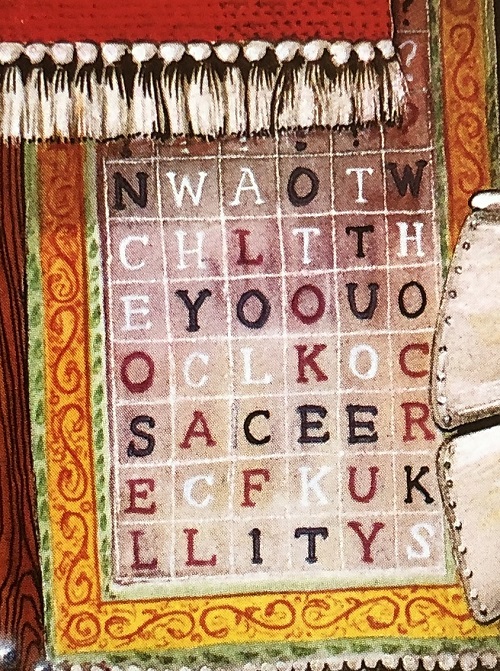
#4
Source: “The Eleventh Hour”
Can a reader solve these challenges? The solutions are known and might even be available somewhere online.
Follow @KlausSchmeh
Further reading: A DES challenge inspired by a conversation with Whitfield Diffie
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Kommentare (4)