A possible solution for the Ohio cryptogram
In 1916, an unknown person robbed a ticket office in Ohio and left behind an encrypted text. The crime and the cryptogram remain equally unsolved to this day. But at least I have a guess as to how the perpetrator might have encrypted.
On June 27, 1916, an unknown man robbed a Western Ohio Railway ticket office in Lima, Ohio. The robber forced a clerk at gunpoint to hand over the contents of the safe. He escaped with $265.
I have blogged and lectured about this story many times before. But before I go into it again today, I’d like to point out my latest publication. Together with Nicolas Courtois and Kacper T. Gradon, I wrote an academic paper titled “Crypto Currency Regulation and Law Enforcement Perspectives”. You can download it here.
The Ohio Cryptogram
Back to the ticket office raid. On July 3, 1916, the local newspaper, the Lima Times Democrat, published an encrypted text that a citizen had provided to the editor. It was of utmost importance to solve this mystery, the accompanying article stated. The reason for the importance was not mentioned, nor was the name of the citizen. The cryptogram read as follows:
WAS NVKVAFT BY AAKAT TXPXSCK UPBK TXPHN OHAY YBTX CPT MXHG WAE SXFP ZAVFZ ACK THERE FIRST TXLK WEEK WAYX ZA WITH THX.
Note that the text contains meaningful words: WHAT, THERE, FIRST, WEEK, WITH, and THX. Apparently, the author left some less important terms in plain text.
A few weeks later, the magazine “Enigma”, published by the National Puzzlers’ League, also published this cryptogram in the August 1916 issue. The rather short article had the following wording:
The police department of Lima, O., is greatly puzzled over a cryptic message received in connection with the robbery of a Western Ohio ticket agent. Here it is: WAS NVKVAFT …
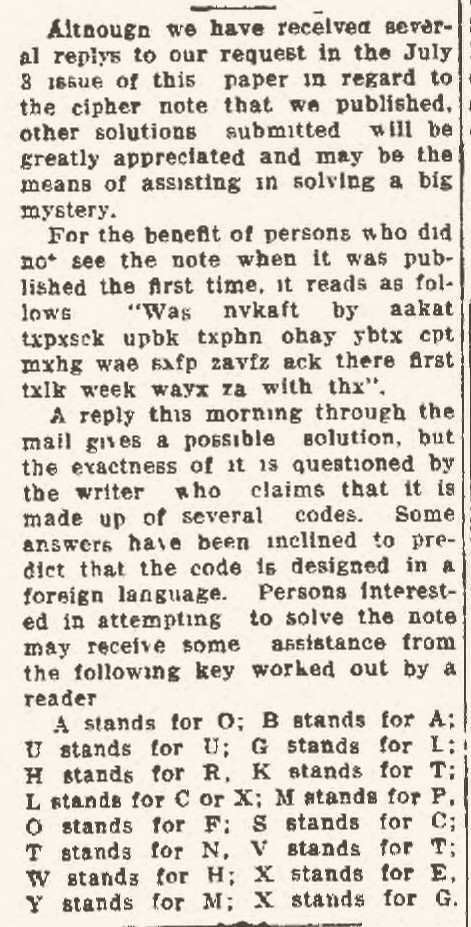
So now it was clear: The cryptogram had a connection to the ticket counter robbery and therefore kept the police busy. Unfortunately, I don’t know what kind of connection there was between the robbery and the cryptogram. The Lima Times Democrat published the first analysis already a few days after the crime. Here it is:
Note that the article contains a replacement table that “might be helpful”. So far, however, this supposed key has not proven helpful at all. In any case, no one has yet managed to crack the encrypted text.
The Ohio cryptogram was brought to my attention at the time by Zodiac Killer expert David Oranchak. Nick Pelling has done some research on the subject and published it on his blog (see here, here and here). You can also read some analysis there.
What is the purpose behind this?
The first question now is what was the purpose of the encrypted message. My guess is that it was an encrypted telegram. Telegrams were sent a lot in those days, and it was not at all unusual to encrypt them.
The second question: what does this message have to do with the crime? If it is indeed a telegram and there is indeed a connection to the ticket booth robbery, then the most likely explanation is that the perpetrator sent or received this message before or after the crime. Perhaps the citizen in question was even an employee of a telegraph company who (for whatever reason) preferred to contact the press instead of informing the police.
Question number three is: What method was used to encrypt the message? Usually, codebooks were used for telegrams at that time, often with an additional encryption (overcoding). In the case of the Ohio cryptogram, the plaintext words that appear in it also speak for a codebook encryption. It was quite common not to look up innocuous terms in the codebook and to leave them in plaintext instead.
How can the puzzle be solved?
A codebook translates each common word in a language into what is called a code group. A code group can be:
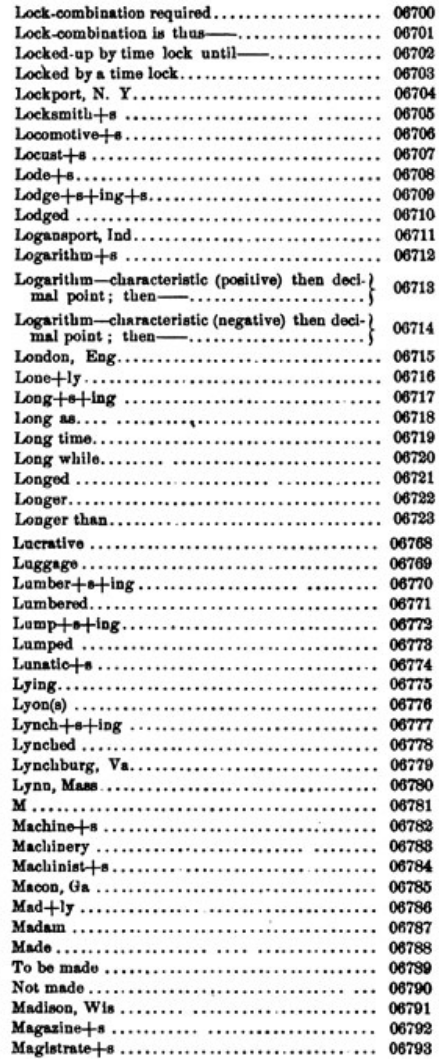
- A number. For example, each code group can consist of five digits, such as 06701. The following scan shows a page from such a code book:
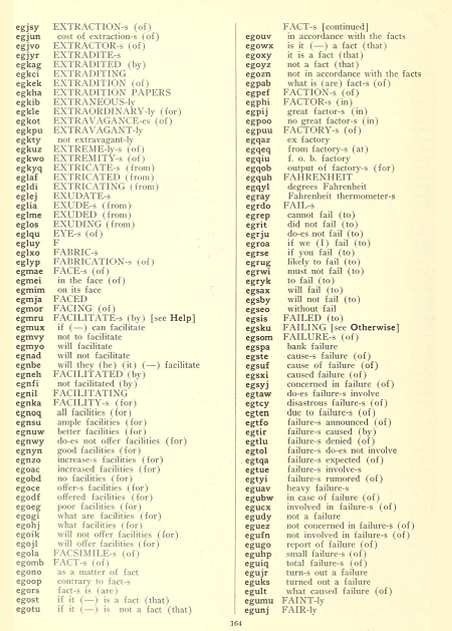
- A sequence of letters. For example, each code group can consist of five letters, such as “egjsy”. Here is a scan from such a codebook:
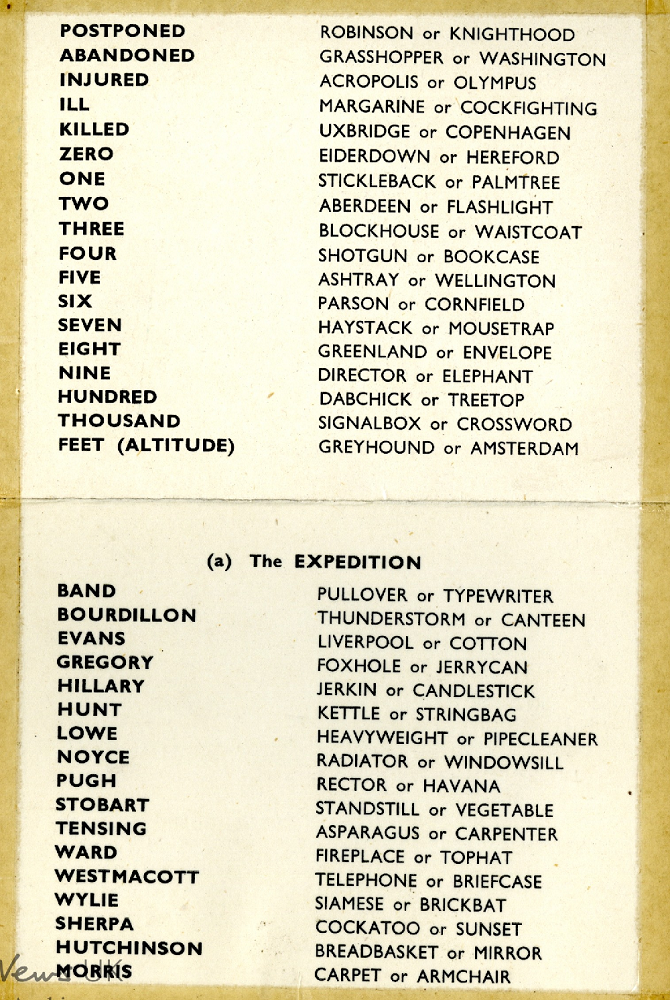
- A meaningful word: Each code group can be a word from any language, but given a completely different meaning. Here is an example:
It is clear that none of these three variants fits the Ohio cryptogram. At most, it would be conceivable that code groups were used which consist of letter sequences of different lengths, but which do not result in meaningful words. However, I have never come across a codebook of this kind.
It would be very well possible that the author of the text used a codebook whose code groups are meaningful words and that he encoded the code groups additionally. This overcoding was widespread. Procedures that could be used for this purpose were often even described in the codebooks themselves.
Mostly these were quite simple methods. For example, to overcode a numeric code group, one could add the current date in each case. So if the code group 081533 is used on August 10, 2021, 100821 is added, which results in 182354. We can consider this type of overcoding as a variant of the Vigenère cipher.
If we assume that the words in the Ohio cryptogram were also created from meaningful words by a simple overcoding, the question naturally arises as to which overcoding method was used. Again, a Vigenère cipher could have been applied to each code group. But what is the key?
At this point I would appreciate feedback from my readers. Does anyone know of an overcoding method that was used a good 100 years ago? Could a computer program be used to test by brute force whether a particular Vigenère encryption applied to each word would produce a result? Are there other approaches to test my conjecture? I will gladly accept comments on this.
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: A gang codebook found in a former prison
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/




Letzte Kommentare