
Vermutlich ist dies der letzte Cipherbrain-Artikel auf diesem Portal. Ich möchte ihn nutzen, um die Goldene Alice 2022 für herausragende Leistungen im Bereich der Kryptogeschichte und des Codeknackens zu verleihen.
David Vierra hat die Challenge von Matthew Brown gelöst. Damit ist er der neue Träger des Friedman-Rings.
Letztes Jahr habe ich über neun verschlüsselte Nachrichten aus dem Computerspiel Noita berichtet. Noch immer sind diese ungelöst, doch es gibt neue Hinweise.
Eine Zeitungsanzeige aus dem Jahr 1893 enthält eine verschlüsselte Passage. Vermutlich ist diese nicht eindeutig lösbar.
Auf Twitter haben einige User ihre verschlüsselten Tagebücher vorgestellt. Die meisten davon dürften nicht schwer zu dechiffrieren sein.
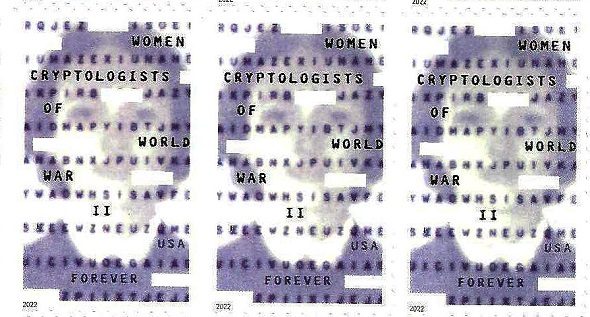
In den USA ist eine Briefmarke erschienen, die die Dechiffriererinnen des Zweiten Weltkriegs ehrt. Auf diesen Marken ist ein verschlüsselter Text abgedruckt.
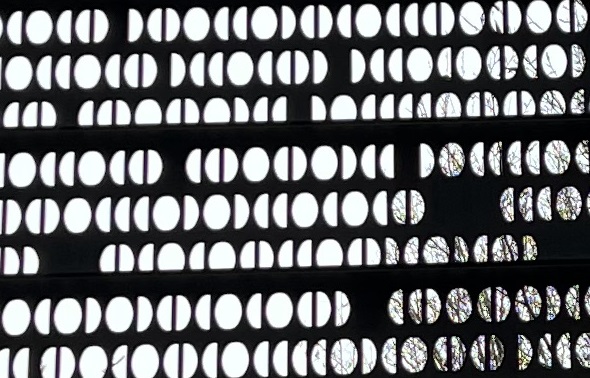
Auf dem Bundeswehr-Ehrenmal in Berlin ist ein Code angebracht, mit dem sich anscheinend noch nie jemand beschäftigt hat. Kann ein Leser die kodierten Botschaften lesen?
Alles wichtige zum Thema Post-Quanten-Kryptogafie auf 25 Seiten – das gibt es in meinem kostenlos erhältlichen Whitepaper “Post-Quanten-Kryptografie – verständlich erklärt”.
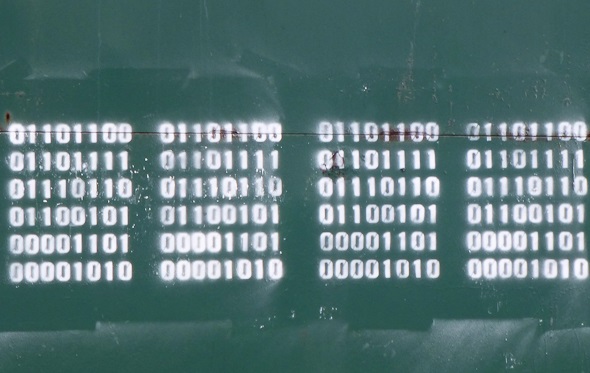
Ein Londoner Künstler stellt auf einer Webseite zahlreiche Graffiti vor, die jeweils eine Binärfolge zeigen. Kann ein Leser diese Nachrichten entschlüsseln?
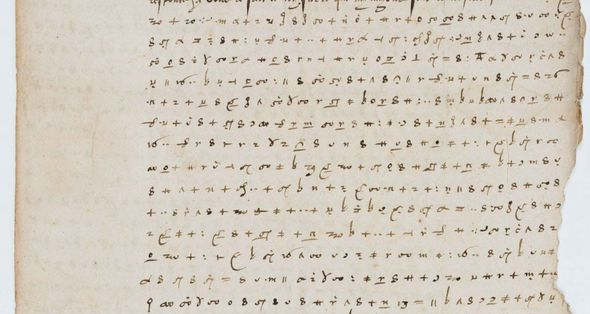
Französische Wissenschaftler haben einen Brief von Kaiser Karl V. entziffert. In der Presse wird dies als Sensation gefeiert.

Letzte Kommentare