The Handycipher is an encryption algorithm that doesn’t require a computer program or a machine. But is it secure?
Handycipher is a low-tech cipher, simple enough to permit pen-and-paper encrypting and decrypting of messages (see part one of this article series). It was published by Bruce Kallick in 2014. The following picture Bruce provided me is a joke, I guess.
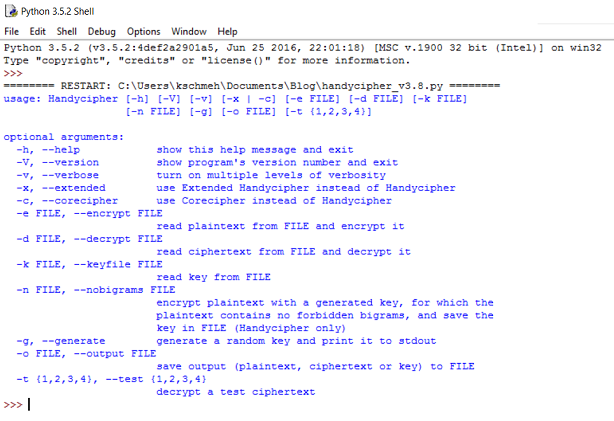
A computer simulation
Bruce has also provided a computer program in Forth implementing Handycipher. As Forth is not so popular, the CrypTool team wrote a version in Python, enhanced with several commandline options (this is they way standard IETF RFCs are created: there are always two independent implementations). The Python version is available here. The file provided for download is a ZIP archive containining another ZIP archive named handycipher.zip, which contains the simulator handycipher_v3.8.py, together with a sample plaintext, a sample ciphertext, and a sample key. To execute the simulator, you need to install a Python application (version 3.x).
Attacks with Hill Climbing
According to Bruce Kallick, the base cipher (i.e. the Handycipher in its simplest variant, not using nulls) has proven remarkably robust when encrypting relatively short plaintexts (less than a few hundred characters). However, with increasing message length it becomes more vulnerable.
As explained in the first article, Handycipher is further strengthened by randomly adding meaningless characters (nulls) to the ciphertext. In addition, Bruce Kallick has introduced Extended Handycipher, which is slightly more complicated than the original version but is also more secure (details are given in the specification).
Frequent readers of this blog will easily guess, which method can be used to attack Handycipher. It’s Hill Climbing, the super-algorithm of classic codebreaking. Codebreaking with Hill Climbing works if small changes in the key cause small changes in the cleartext. This is the case for many manual ciphers, including Handycipher. Detailed information about attacks on Handycipher are available here and here.
Challenges
On the cipher puzzle portal MysteryTwister C3 some 20 Handycipher challenges are available:
- Six challenges address a weakened Handycipher version.
- Nine challenges are dedicated to the standard Handycipher.
- Six challenges are about the Extended Handycipher.
According to Bruce Kallick, the first and only MTC3 participant who has solved all Handycipher challenges is George Lasry, a well-known codebreaker and reader of this blog. The following picture of him was taken in Smolenice.
George cracked the last Handycipher challenge only a few days ago. It comes as no surprise that he used Hill Climbing to solve the challenges. He wrote to Bruce: “It is very similar to solving a Playfair square, with the addition that you must put apart the nulls.” I hope, George will publish a few details about his attacks soon.
Does George’s work prove that Handycipher is a weak encryption algorithm? Not necessarily. Experience shows that it is as good as impossible to develop a cipher that is simple enough to be used manually, but still is as secure as a modern encryption algorithm like AES.
The last (and hardest) Handycipher challenge on MTC3 requires breaking a ciphertext consisting of over 7000 characters. It is clear that typical ciphertexts used in practice are much shorter, say a few hundred letters. It has yet to be found out if a Handycipher cryptogram of such a length can be broken. I am looking forward to additional research in this field.
Follow @KlausSchmeh
Further reading: How Paolo Bonavoglia and Bart Wenmeckers solved a an early 20th century cryptogram
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/



Kommentare (3)