20 years ago, Jim Gillogly, a great codebreaker and reader of this blog, created three crypto challenges – a Playfair, a Double Playfair, and a Double Column Transposition. Can you solve them?
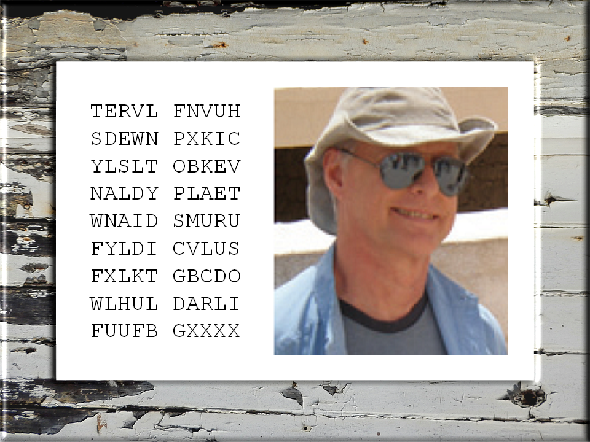
Frequent readers of this blog certainly know Jim Gillogly. Wikipedia introduces him as “American computer scientist and cryptographer”, whose “interest in cryptography stems from his boyhood, as did his interest in mathematics. By junior high he was inventing his own ciphers and challenging his father, entomologist Lorin Gillogly, to solve them.” Already in 1970 Jim (born 1946) wrote a chess-playing program.
Among cryptologists, Jim is best known for having solved a number of notable cryptograms. In 1980, he wrote a paper on unusual strings in the Beale Ciphers, and he received international media attention for being the first person to publicly solve the first three parts on the famous Kryptos sculpture. In 1995, he deciphered a text enciphered by Robert H. Thouless, who had hoped the message could prove that the dead could communicate with the living. His most extensive codebreaking project was the deciphering of several hundred IRA messages from the 1920s.
Last but not least, Jim is a reader of this blog, which I am very proud of.
The challenges
A website hosted by the TV channel Nova contains a text Jim wrote almost two decades ago. It is titled “Crack the Ciphers”.
In this publication Jim introduces three crypto challenges. In all three cases the cipher algorithm used is known, which means that one needs to find the key in order to solve the challenge. The algorithms Jim used should be well known to the readers of this blog: the Playfair Cipher, the Double Playfair Cipher, and the Double Columnar transposition. All three ciphers are known to be quite secure but not unbreakable.
Cipher #1 (solution known)
Cipher: Playfair (check here for Jim’s explanation of this cipher)
VYTES YEDLU TERVL FNVUH DWARD LCFFB SDEWN PXKIC
FTREO LKALZ YLSLT OBKEV LYARM KRBOD NALDY PLAET
OLQAD FHSFZ WNAID SMURU OLHRY LLOTW FYLDI CVLUS
VSSFZ YLUNF FXLKT GBCDO BFALE WRPFY WLHUL DARLI
TFLAB FFZCY FUUFB GXXXX
According to Jim’s article, the phrase “beware ice weasels” appears and the phrase “red penguin frenzy” might appear in the plaintext. The sender used “STOP” between sentences and “END” at the end.
Five people solved this challenge back in 1999. You can read their solution descriptions here.
Cipher #2
Cipher: Double Playfair (check here for Jim’s explanation of this cipher)
TYINP KPQOT YENSO IYOBO YRAKK SLSPP ZCDOA YSLPO
MXMNP PNXPT YCITT YQYBO ZRBIG MPLSE ZKCTX RCRQG
LEIKC RDMPP RTBNX WYWQG MDAYT GFVMF XEYSL LQNII
GIWRQ IGFEV NGDNN IOBDT MDPTT YXNKB UXEMW PPKPW
ST
Jim writes: “Earlier messages in this format have been in English using the Double Playfair system. They used “STOP” between sentences and “MESSAGE ENDS” at the end. Unfortunately, we can make no further guesses about the content. The earlier messages have occasionally re-used Playfair squares; keywords used recently include DUNDEEMARMALADE, YORKMINSTER, BRIGHTONROCK, and BLARNEYSTONE. Previous messages suggest they are planning a coordinated sabotage effort later this year.”
Cipher #3
Cipher: Double Columnar Transposition (check here for Jim’s explanation of this cipher)
TADTN TPLIE RCENI SIITD ONMUN MTNSO LDMMB ENROH
SETLV EACES BCSNT OVDAR YSIST ENNES SFAOE SFNAT
UWHSO FLSGR TLUDG ETONI CRGLD ELIIR AETTP DHUDD
IOPHW FISOT ISOIV EDSSN TWOAO RESSA RSHEU NATNS
GOSRP RDIFN ESEEO ADUPT IRRSE PPRHM EMHVU NOIRO
DSEFR MCIIE
Jim writes: “Based on her [the sender’s] poem and schedule I believe she should have used MAHATUNDILA and CULLATINDILA as her double transposition keys, but these do not result in a correct decryption. Please try the usual variations—keys in wrong order, columns interchanged, one key left off, and so on.”
How to solve the challenges
As mentioned, the first challenge was solved by five readers of Jim’s article back in 1999. The other two remained unsolved. The solutions of these are not provided on the Nova website, and I don’t know any other source that mention them. So, perhaps my readers can solve them.
Breaking these two ciphertexts should be considerably easier today than in the 1990s. Meanwhile, several helpful cryptanalysis tools, like Cryptool 2, are available. In addition, many codebreakers have developed their own codebreaking programs. Thanks to the publications of George Lasry and others, the breaking of a Double Column Transposition is today much better understood than twenty years ago. Perhaps, some of the codebreakers among my readers already know these challenges and have solved them.
In any case, if you know one of the solutions, please leave a comment.
Follow @KlausSchmeh
Further reading: The world record crypto challenge
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/



Kommentare (4)