Peter Nüchterlein, the writer-in-residence in Wernigerode, Germany, has asked me for help. In a Vienna archive he has found over 100 encrypted documents from the Thirty Years’ War. Today, I am going to introduce five of them. Can a reader decipher them?
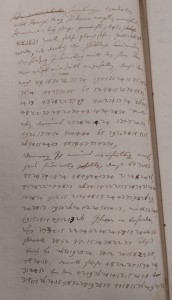
Last week, I received an email from Peter Nüchterlein, the writer-in-residence in Wernigerode, a town in the German state of Saxony-Anhalt. He wrote: “In the course of my research on the Thirty Years’ War, I have recently viewed and partly photographed several thousand archive pages in the Vienna Court Archive. There are a dozen or so pages with a numerical encryption code, nobody in the archive could decipher. It is a mixed text of German sentences and numbers.”
It goes without saying that I suggested to publish these findings on my blog. Mr. Nüchterlein agreed. Meanwhile, he has even found over 100 encrypted pages (mainly letters) in the material he copied. These letters were written by ministers to the Austrian emperor. Mr. Nüchterlein believes that at least four different encryption methods have been used. Today, I am going to introduce excerpts from five documents that are encrypted in one of these methods.
Some readers will remember that last year blog reader Thomas Ernst solved a number of encrypted letters from the Thirty Years’ War. Two years ago, blog readers Christoph Tenzer and Thomas Bosbach broke a cryptogram created by Albrecht von Wallenstein in the same time period. This proves that some of my readers are quite experienced in cryptanalyzing cryptograms from the 17th century. I’m optimistic that the solution of the ciphertexts Mr. Nüchterlein provided me will be found, too.
Five encrypted passages
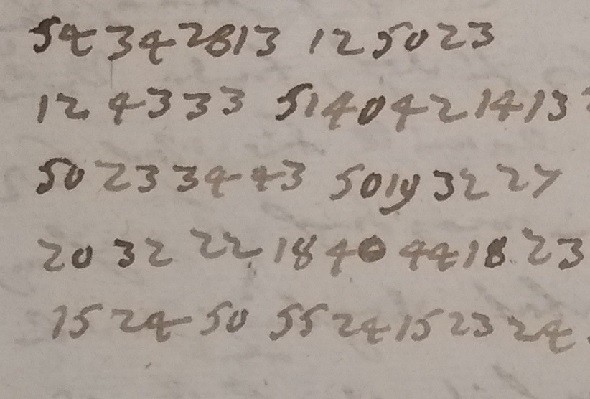
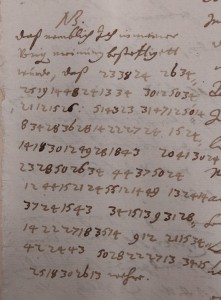
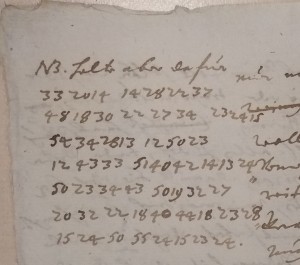
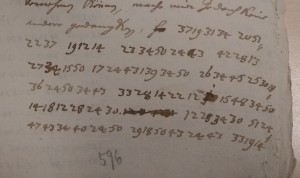
Here are the five excerpts:
#1
#2
#3
#4
#5
Solution approaches
As can be seen, every encrypted word consists of an even number of digits, like 332014 or 2234. This means that we probably deal with an alphabet consisting of two-digit numbers. In other words, 332014 needs to be read as 33/20/14, while 2234 is actually 22/34. The Wallenstein cryptogram mentioned above is written in the same style. The cryptogram also contains a number of commas and colons.
As far as I can see, none of the two-digit numbers appearing in the cryptogram is greater than 60. This means that we probably deal with a letter substitution that includes a number of homophones or nulls or phrases.
Can a reader break this encryption? I am sure, Peter Nüchterlein will be very thankful for a solution.
Follow @KlausSchmeh
Further reading: How Edgar Allan Poe broke about 100 ciphertexts
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/



Kommentare (21)