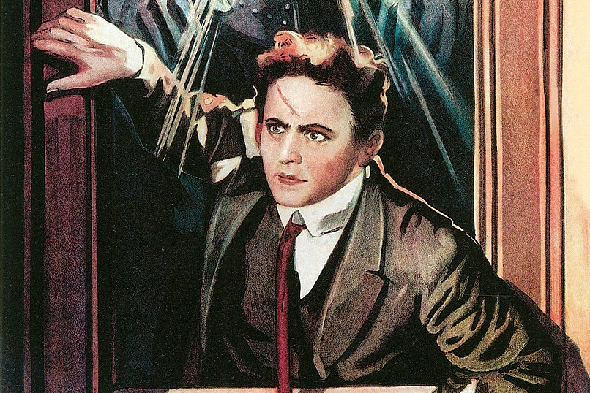
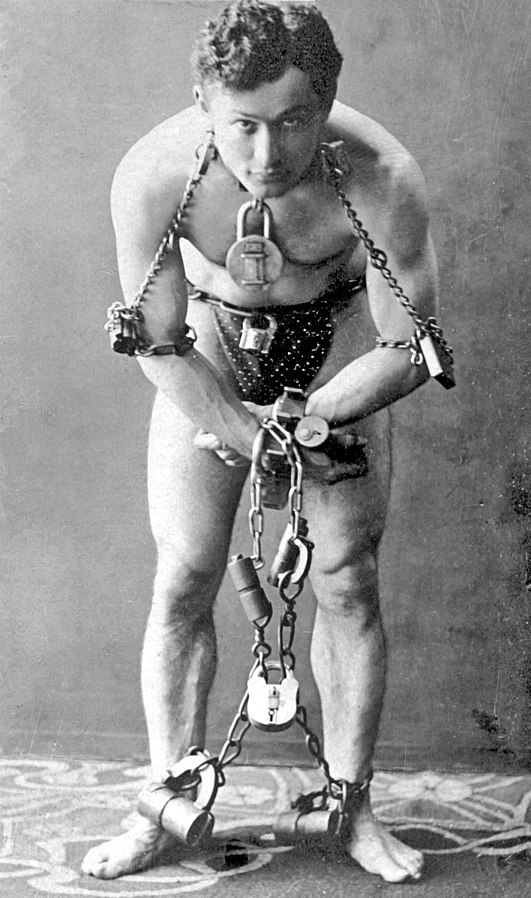
Harry Houdini (1874-1926), illusionist and pioneer of the skeptics movement, had an interest in ciphers. Can you solve two encrypted telegrams he mentioned in one of his essays?
Harry Houdini (1874-1926) was an American stage magician and stunt performer, best known for his spectacular escape acts. Born Erik Weisz in Hungary, he started his career in the United States and later toured Europe, where he escaped from bonds (“Handcuff Houdini”), straitjackets, and locked cabinets.
When Houdini’s mother died in 1913 of a stroke, this proved a shock for him. With the help of psychic mediums, he tried to contact her in the beyond, but soon realized that none of these people really really had the power to do so. Once, a clarevoyant presented Houdini a letter she had allegedly received from his mother, transmitted from the realm of the dead – but the message was written in English, a language this woman had never spoken.
Based on these experiences, Houdini began investigating the methods of psychics and became a fanatic critic of paranormal claims. He emphasized that his own magic performances were based on tricks, not on supernatural powers, though some – including Sherlock Holmes author Arthur Conan Doyle – did not believe him.
Today, Houdini is regarded as a pioneer of the skeptics movement, having influenced numerous other illusionists who also engaged in challenging paranormal claims. In the USA, James Randi and Penn & Teller are the most notable of these, while in Germany stage magicians Wolfgang Hund (Hundini), Peter Schütte (Ergie Wäggedawn), and Eckart Taglinger (Meister Eckart) are active members of the skeptics community.
Houdini’s crypto treatise
In David Kahn’s well-known crypto history book The Codebreakers, I read that Houdini had an interest in ciphers. He even wrote a short essay about codebreaking, which is today available in the book Houdini on Magic. Here are a few paragraphs from this treatise:
My first introduction to the world of cryptography occurred about twenty years ago when, not having enough money to wire home for my return fare, I was stranded with a small touring company in Chetopa, Kansas. I wished to leave that beautiful city as fast as the inventions of mankind would permit me. But alas! I lacked sufficient money with which to buy a postage stamp, let alone railroad fare, so I went to the telegraph office to send a message “collect at the other end.” […]
While I was waiting, an old man walked into the office and handed in a message, paid for it, and left the office. No sooner was he gone than the operator called me to him and said, “Here, you magician, tell me what this means. I shall never forget the message; it was of such a nature that it is almost impossible to forget it. The operator looked at me with a smile and said that he would send the message and then allow me to study it while I waited for my answer.
I was in that office at least five hours, and to that wait I am indebted for my ability today to read almost any cipher or secret writing that is handed to me. I have made quite a study of this art, and often it has been the means of giving me a friendly warning or clever hint to look out for myself.
The message that I studied in that grim telegraph station was written as follows:
“XNTQLZCXHM FOKDZRDQDS TQMZRJGDQ SNEN QFHUDE ZSGDQ.”
I managed, after some worry, to solve the message, and very few things in after life gave me as much pleasure as did the unraveling of that code. […]
The telegraph operator seemed to think that this was a great feat, and even while we talked about it the answer arrived:
“BZTFGSDWOQ DRRZQQHUDMNN MXNTQKHSSKD ZKHBD.”
[…]
This was my debut as a cypher-ist. Since then I have picked up the newspapers and have never failed to read any and all cyphers printed in the personal columns. Sometimes, I have in a joking manner answered their cypher and signed myself “Roger Bacon,” as he was the first I know of to make use of this method of varying the alphabet.
[…]
Our second sight artists were the first to utilize the code or cipher for exhibitions. They had secret signs, movements, and questions in which they conveyed their answers or information to the medium. […]
Roger Bacon thought so much of cryptography that he classed it under the name of cyphers as a part of grammar. The Lacedemonians, according to Plutarch, had a method in which a round stick is made use of. John Baptiste Porta (1658) also described this method, so I will show the reader just what there is in it. This method is sometimes attributed to Archimedes but as to that, I am in no position to argue one way or the other. For this system, you must obtain two round sticks, one being in your possession and the other in the possession of the person to whom you wish to send your message. A long and narrow strip of paper, say ticker tape, must be wrapped or rolled spirally across your stick or cylinder. Now write your message right across the strips. When unrolled, the slips of paper seem to signify nothing. These wooden sticks are known as Scytala Laconias.
[…]
The method of using numbered squares is sometimes called the checker-board system, and with this method, you can arrange almost any code in the world, using any article, places, or characters, as you simply use the checker board as your guide, and arrange everything accordingly.
It is possible to hold a conversation by knocks on the walls of cells, but in America, where they seldom have solid walls in prisons or station houses, it is sometimes used by holding up figures and spelling out the words, although the deaf and dumb alphabet is far better, but harder to learn. I mean by that, it can’t be learned in the first lesson, while with a chart, this checker board is a very easy matter. Criminals have their own hieroglyphics, in fact you
will find secret signs and marks in almost every path of life.
[…]
To give you an idea of how important the letter “e” is in all writings, the following inscription over the Decalogue in a country church runs as follows:
PRSRVYPRFCTMNVRKPTHSPRCPTSTN.
It is stated that this was not read in over two hundred years, but if you will insert the letter “e” in a good many spaces, you will be able to read, “Preserve, ye perfect men; ever keep these precepts ten.”
The two encrypted telegrams
Let’s look again at the two encrypted telegrams that are mentioned in Houdini’s essay:
XNTQLZCXHM FOKDZRDQDS TQMZRJGDQ SNEN QFHUDE ZSGDQ
BZTFGSDWOQ DRRZQQHUDMNN MXNTQKHSSKD ZKHBD
The easier question now is how these messages can be deciphered. The more difficult one is why the telegraphy clerk handed these ciphertexts to Houdini, although he certainly knew that this was against the law. I can hardly imagine that such a person was not familiar with the secrecy of letters and correspondence principle.
If a reader knows the answer to either of these questions, please leave a comment.
Follow @KlausSchmeh
Further reading: The Top 50 unsolved encrypted messages: 38. The Sufi Fiddle mystery
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/




Kommentare (5)