Kryptos, the Fenn Treasure and a Mathematical Puzzle
Today it’s about four interesting letters on different topics that I received from blog readers. I hope that one or the other discussion will get going.
As you can imagine, I often receive letters from readers. Some of them are so exciting that I immediately make a blog article out of them. On the other hand, of course, I also receive numerous less interesting e-mails and those that do not lead to a blog post for other reasons.
And then, every now and then, there are letters that fall into neither category. Today I’d like to share four of them. All four reader emails are interesting, but have not yet led to a blog article because the topic is too specific or not crypto-relevant.
Georg Herrmann on a possible crypto-mystery
Blog reader Georg “Schorsch” Herrmann wrote me the following:
Enclosed is a mail that came to my attention two years ago – under somewhat obscure
circumstances – has come under:
Received: from mta2.sender (mta2.sender [217.23.139.xxx]) by mail.receiver (Postfix) with ESMTP id 74B6E48301 for <>; Wed, 31 Jul 2019 12:15:04 +0200 (CEST) DKIM-Signature: v=1; a=rsa-sha1; c=relaxed/relaxed; s=default; d=sender; h=Content-Type:MIME-Version:From:To:Subject:Date; i=noreply@sender; bh=XpMy56kVm29qzxkqmxzhO7XayTM=; b=ZOpWNOVgdQhvykHMS+6UjAW3V080KP49uDybHlYSeCUXfdrn0JEqMtaj4abyi0m2BK3XJRzJ0LDO fWFdqpEPWOjpMC1LAcfj6woQiWJqFzNcDt3/oCS2hLU4rUUOicAbBHPtB2b6l6axpdMHB6vD/7JN Rq8WanVd/5/uCI6veJg= Content-Type: multipart/alternative; boundary="===============8284055664131553004==" MIME-Version: 1.0 From: <noreply@sender> To: address@receiver Subject: YRZXSZRRO PZJLRRUAM Date: Wed, 31 Jul 2019 10:10:25 Precedence: bulk Mesage-Id: J226CYM6II6XG8H Unsubscribe-link: https://GZNJTPC18C2J2L0/unsubscribe Message-Id: <20190731101506.A4D9148303@mail.receiver> --===============8284055664131553004== Content-Type: text/html; charset="us-ascii" MIME-Version: 1.0 Content-Transfer-Encoding: 7bit O 15WMZSIY QWLZAP1JWA0J3SMJJ IRDWS2NS68LSNO0 7JXVB G1IUBUV2D3IH83HJ1UZRRMDN2HDI2LHSJJRC9DOS780X SGDI --===============8284055664131553004==--
I have removed all data that could be used to identify the sender or recipient. The sender’s domain in Russia no longer exists, but it did at the time. The sending server belongs to the Russian data center operator Rusonyx Ltd. in Moscow, which rents out virtual servers, among other things.
The German recipient and his personal circumstances are known to me to some extent, a connection to Russia exists insofar as the recipient is active in international freight traffic.
The mail contains – apart from the typical cryptic DKIM signature – already in the header three fields which seem to contain encrypted data, namely:
– Subject: YRZXSZRRO PZJLRRUAM
– Mesage-Id: J226CYM6II6XG8H
– Unsubscribe-link: https://GZNJTPC18C2J2L0/unsubscribe
Of this, the recipient usually only gets to see the subject. In automated processing, however, the data obfuscated in the mesage ID (sic) and unsubscribe link could be processed as well –
for example, they could serve as a key.
The mail text consists of three lines:
O 15WMZSIY QWLZAP1JWA0J3SMJJ IRDWS2NS68LSNO0 7JXVB G1IUBUV2D3IH83HJ1UZRRMDN2HDI2LHSJJRC9DOS780X SGDI
Whether this is actually encryption, or mere data garbage – I have no evidence to prefer one assumption or the other.
If it is encryption, this mail may not be addressed to the person himself, but serves as a control instruction to a program on the recipient’s PC or smartphone. However, I personally do not know of any case where a control server would communicate with a bot in this way.
The fact that some misconfigured spambots produce data garbage is an everyday occurrence. I encounter such mails every day. But this mail stands out, this is not the data garbage I usually know.
Most likely this mail reminds me of deliberately cryptic mails, with which some (5, 6, 7, ???) years ago the recipients should be misled to buy penny stocks, i.e. stock prices should be manipulated. After some thought, they were quite easy to decode (otherwise they would not have reached their goal), and above all, these mails were really sent en masse at that time, whereas this is a one-off.
Pollo about a mathematical-historical puzzle
The blog reader Pollo sent me the following hint:
In an article Martin Vieweg writes about evidence of applied mathematics 3700 years ago in Babylon. The mathematician Daniel Mansfeld also examined a clay tablet, the back of which shows numerals, which he could not fully explain until now. The author quotes him at the end of the article as saying: “So far I cannot figure out what they mean. I’m very interested in discussing with historians or mathematicians who might have an idea what these numbers are trying to tell us!”
You and your resourceful community are actually predestined to step in to help, aren’t you?
Here is the original article from the Australian University (UNSW Sydney).
Christian Wasserbauer on the Forrest Fens Treasure
Blog reader Christian Wasserbauer from Austria has thoughts on Forrest Fenn’s poem and treasure:
Initially, I could not appreciate this story much because I thought this was just a marketing stunt.
But then I took a closer look at the poem after further blog posts and I have to say that the choice of words and the wording of the poem is partly interesting. Especially when you consider that Forrest Fenn, as he himself claimed, spent over ten years thinking about his poem. If the poem was really “constructed” so carefully, its wording should not be random.
Since Forrest Fenn mentioned that knowledge of encryption techniques is not an advantage in the solution, encryption in the classical sense is already ruled out. I also think that a direct description of the way is rather improbable. For 10 years a lot of people have thought about this poem. As far as I know, most of them have followed the approach of a direct description of the way. So if the whole thing was not a hoax, I think the treasure should have been found much earlier. However, to my knowledge, not even a logical starting point was found until the end.
So I took a look at the poem assuming it was a mystery.
The first clue, according to Forrest Fenn, is the line, “Begin it where warm waters halt.” Since the plural is used, it’s probably about a lot of water. Perhaps even all the surface water of the earth. This, when warmed by the sun, stops above our heads in the form of clouds. The wind may move the clouds, but the water still stops up there before it falls back down. This would also explain why Forrest Fenn kept mentioning Eric Sloane. Eric Sloane had a soft spot for the sky and meteorology. He was famous for his cloud paintings and founded the first, televised, weather report in the US.
For “not far, but too far to walk”, there are actually not so many possibilities. Because if you take it exactly, even 1000km are not too far to walk. However, 1000km is already far, at least for earthly distances. Now “not far, but too far to walk” could perhaps stand for a geological hurdle, such as water or rock cliffs, which make a short distance impassable for our feet. But my favorite here is a distance in time. This is a metaphorical canyon in which there is only one direction. And since sun-made clouds are created during the day, a logical short distance, would take us into the night.
Again, time would be an explanation for Forrest Fenn’s many mentions of Albert Einstein.
Now, when we look up at the sky at night, we see the stars. One of the largest and best known constellations is the Great Bear. The biggest bears are the brown bears. Only polar bears can grow bigger, but not so massive. And polar bears are closely related to brown bears. Since the singular is used in this case, there should be only one brown. There is also the constellation Little Bear, but little bears are rather e.g. black bears or panda bears. It is also known that Forrest Fenn liked to be outside at night and admire the night sky. So maybe the “Big Sky” is the home of the brown bear.
Forrest Fenn’s statement that an Indian girl with only his poem and a map at her disposal cannot solve more than the second clue would also fit well here. For although the 88 constellations were finally established by the IAU in 1928, they have not caught on everywhere. The Great Bear does not exist in India. Only the bright stars of the Big Dipper are known as Saptarishi. Which means “the seven prophets”. Northwest of Yellowstone National Park there is a region called Big Sky. Perhaps one needs to continue south of there.
The word “meek” is usually used incorrectly in English. Most people use it to mean fearful or timid, but it actually means meek or patient. Now, since Forrest Fenn supposedly thought about the poem for years and chose each word very carefully, he should have known what “meek” really meant. “The meek” could perhaps be the buffalo. When these leave Yellowstone National Park in winter in search of food, the farmers drive them back or shoot them. This is because the farmers are afraid that the buffalo will infect their animals with brucellosis.
“Your creek” could then stand for “Buffalo Creek.” The “Buffalo Creek” is full of boulders and logs and covers almost 1000hm on its way. It flows into the Slough Creek at the Slough Creek Campground of the Yellowstone National Park. The semicolon that separates the third stanza into two parts would also make sense here. This would at least put us in the region that meant a lot to Forrest Fenn.
Then, with “If you’ve been wise and found the blaze,” the poem suddenly switches to past tense for one line. Again, if one is accurate here, the “blaze” (which can indicate not only a flame but also a marker) has already been found at this point and would be Buffalo Creek in my case. Forrest Fenn’s statement that the “blaze” points neither N, E, S, or West would thus also be valid. Perhaps the word “blaze” was used here primarily because it basically fits at this point to point to a marker and also because it needed a word that rhymes with “gaze” in the line after next.
With “Look quickly down, your quest to cease,” the poem now switches back to present tense.
The best I can come up with for this line is to keep looking south of Buffalo Creek and/or from a bird’s eye view.
In the next line, things get exciting again with “But tarry scant with marvel gaze,”. At first glance, “tarry scant” is used here to describe a brief lingering. But first, this phrase is very unusual, and second, “tarry scant” doesn’t make sense as a filler at this point either, because it doesn’t rhyme with anything. Now, if it doesn’t rhyme anyway, Forrest Fenn could have simply used a better choice of words for a short tarry. But apparently the word “tarry” is important at this point. Since tar is an extremely viscous substance, “tarry scant” could stand for an even much slower movement, e.g. plate tectonics. If you combine this with “marvel gaze”, this might be a lake that looks like an eye from a bird’s eye view. About 2km southeast of the mouth of Buffalo Creek, there is a small lake that, with imagination, looks like an eye moving very, very slowly.
For the fifth verse I have again no ideas.
With “So hear me all and listen good,” I then only remember that one needs both ears, which are approximately mirror-image, in order to listen well. 150m west of the lake is a marshy area, which is smaller, but a mirror image of the lake.
“Your effort will be worth the cold.” might tell you to shift your attention to the marshy basin, where something is hidden in the wet mire.
Since “brave” also stands for defying something, I thought maybe “If you are brave and in the wood” stands for something rising out of the forest of long marsh grass, e.g. a big stone. And a large stone does indeed rise out of the long marsh grass to the northwest of the marsh (44°56’02.8 “N 110°17’35.5 “W). That would make a total of nine clues pointing the way.
I made a detour to this spot in July 2019 while passing through. However, I was unfortunately short on time at the time and wanted to check out Mammoth Hot Springs as well. But even though this little swamp didn’t seem to be particularly deep, I don’t think anyone would sink a box there. Because searching would be very tedious despite the shallow depth and confined area (around the rock). A metal detector would be an advantage, but it is forbidden in Yellowstone National Park.
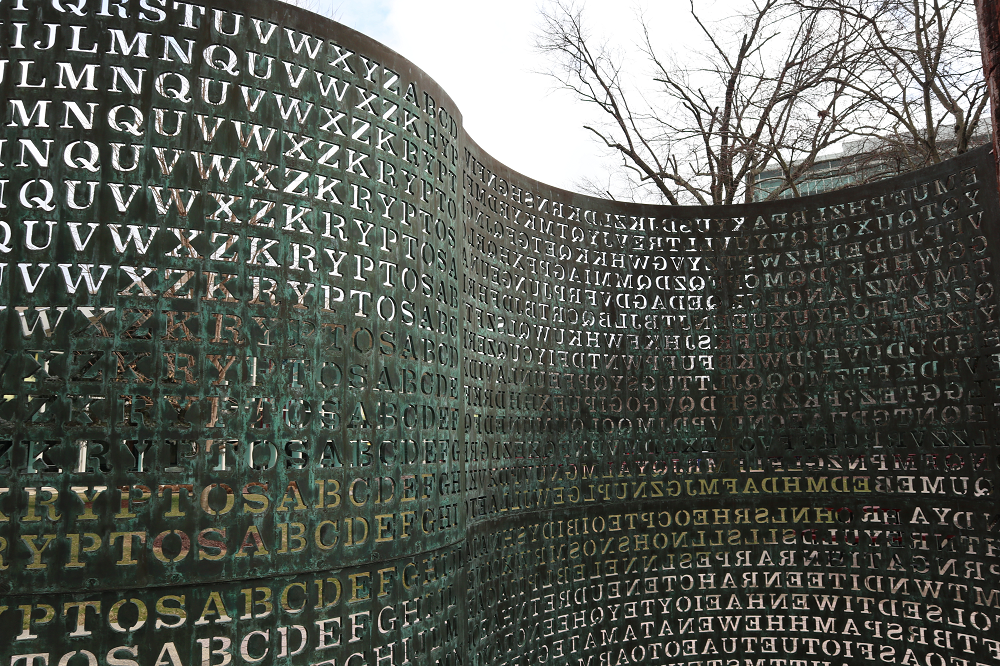
Geoffrey Caveney about Kryptos
And finally, I would like to present the thoughts of Geoffrey Caveney au New York on Kryptos:
I am a math and English tutor in New York City, and in my spare time, when I am not playing chess, one of my hobbies is to research cryptographic puzzles such as the 4th and final message on the Kryptos sculpture.
I strive to base my research and investigation into Kryptos on a sound and rigorous methodology with a strictly statistical basis. To that end, I would like to share with you a striking statistical anomaly that I have found in the course of my research, which I believe may have some real significance for the actual solution of the 4th message of Kryptos.
It seems natural to me to consider such encryption methods as Playfair and Four square as one very possible key step of Kryptos 4. Such bigraphic encryption methods are the one major type of classical cryptographic cipher not yet seen in the other three Kryptos messages. It seems to me that there should be at least one Polybius square employed in one of the Kryptos message encryptions.
The ? before the 97 letters of Kryptos 4 makes a bigraphic cipher with 98 characters natural enough. Playfair is typically ruled out because of the many double letters in the Kryptos 4 ciphertext, but it is striking to me that when the entire message is split in half, in 2 blocks of 49 characters each, and the letters are paired up in order, there are no double letter pairs.
Of course there are numerous possible logical and thematic keywords for any encryption step of Kryptos 4, but it must be recognized that the sequence “DYAHR” does stand out at the beginning of the 3rd Kryptos message ciphertext itself. As a Polybius square keyword, it even neatly places each letter in DYAHR at the top of its own column.
I have long thought that a very logical and thematic clever extra twist to any Polybius square encryption method would be to shift each plaintext letter within the square by a certain number of rows and columns before performing the final encryption step. I think this could very well be the possible “masking step” that Ed Scheidt has referred to on occasion. One would simply need a logical but hard to guess basis for selecting the sequence of numbers 0-4 for the row and column shifts for each letter in the message before the Playfair encryption step.
Out of curiosity, I took the Kryptos 4 ciphertext and performed a Playfair decryption step on it, paired up in 2 blocks of 49 characters as described above, using a Polybius square with keyword DYAHR. Then I compared the resulting text to the crib clues in the plaintext message that Jim Sanborn has revealed: EASTNORTHEAST and BERLINCLOCK. I found that the necessary row and column shift numbers to make the letters in these words shift to the text which then produces the Kryptos 4 ciphertext upon Playfair encryption have the following statistical distribution:
0 shift: 11
1 shift: 14
2 shift: 14
3 shift: 6
4 shift: 3
While such a distribution of 48 values 0-4 could be random, the extremely small number of 4’s and also quite small number of 3’s is striking, and suggests that perhaps this distribution is not random but rather the result of some intentional process.
A natural feature of the Kryptos sculpture text to consider as a possible basis for selecting such a sequence of values 0-4 are the number of characters in each line of the 3rd Kryptos message ciphertext. Unlike the nearly symmetrical line lengths (by number of characters) in the panel of the first two Kryptos message ciphertexts, the Kryptos 3 number of characters per line are “jagged”: 32, 30, 31, 30, 32, 30, 32, 31, 33, 29, and then the remaining lines of Kryptos 3/4 are evenly 31 characters each.
If these line lengths are somehow the basis of selecting the sequence of row and column shifts of the plaintext letters within a Polybius square before encryption, as described above, I observe that there is a parallel between the small number of 3 and 4 shifts before the Playfair encryption with keyword DYAHR and the single lines of Kryptos 3 that contain 33 characters (= 3 modulo 5) and 29 characters (= 4 modulo 5).
One natural method to select the lines of the Kryptos 3/4 panel, and thus the values 0-4 from their line lengths modulo 5, is to use the alphabetical left-hand column of the Vigenere tableau panels as an input key for row selection. That is, any letter can be found in this alphabetical column, and then the line length modulo 5 of the corresponding row in Kryptos 3/4 can be selected as the row or column shift value 0-4.
Of course the lines of Kryptos 3/4 only correspond with the N-Z part of the alphabetical column in the Vigenere tableau panel. But there are some natural ways to map any letter A-M to the line lengths of Kryptos 3/4 as well: The method I prefer is to reflect the A-M rows downward in a mirror image, so that A=Z, B=Y, …, M=N, etc. The biggest advantage of this method is that E maps to the V line = 33 characters = 3 modulo 5.
Now I must admit I find the following statistical occurrence rather remarkable: If one selects 24 letters at random from the Kryptos 1/2 ciphertext, and also 24 letters at random from the Kryptos 3 ciphertext, and maps each letter to the alphabetical column of the Vigenere tableau and then to the Kryptos 3/4 line lengths modulo 5, using the reflective mapping of the alpha column A=Z, etc., the expected distribution of the resulting values 0-4 is as follows:
0 shift: 10.3
1 shift: 13.7
2 shift: 13.7
3 shift: 6.5
4 shift: 3.8
I find it quite remarkable to find the close correspondence of this distribution with the actual observed distribution of the row and column shifts necessary to make the letters in EASTNORTHEAST and BERLINCLOCK shift to the text which then produces the Kryptos 4 ciphertext upon Playfair encryption with the text letters paired in two halves of 49 characters each using the Polybius square with keyword DYAHR.
Unfortunately, I have not yet been able to find any logical way to select actual letters from the Kryptos 1/2 and Kryptos 3 ciphertexts that produces any sequence of actual row and column shift values 0-4 in an order that matches up exactly with those necessary for EASTNORTHEAST and BERLINCLOCK. The challenge is that there are so many possible ways to make such a selection of 97 letters from Kryptos 1/2 and 97 letters from Kryptos 3 that it is difficult to know where to begin or how to approach the search for the correct selection method in any kind of systematic manner.
But the extraordinarily striking close correspondence of the distribution of the 0-4 shifts that I have described above gives me an objective statistical reason to believe that maybe, just maybe, my approach may possibly be on the right track.
Conclusion
All four letters contain interesting thoughts that I unfortunately cannot go into in detail here. Anyone who would like to comment on them is of course welcome to do so in the discussion forum. Perhaps one or the other fruitful discussion will get underway.
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: Vom Teddybär bis zum Weihnachtsbaum-Anhänger: die schönsten Merchandising-Produkte der NSA
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/



Letzte Kommentare