Three more unsolved ciphertexts from the battle ship Schleswig-Holstein
In September 2017, I blogged about an encrypted message sent in 1939 from the Schleswig-Holstein, a German battleship, to a private address in Kiel. This cryptogram has not yet been solved. Thanks to blog reader Patrick Hayes, there is now (fairly extensive) new information about this crypto puzzle.
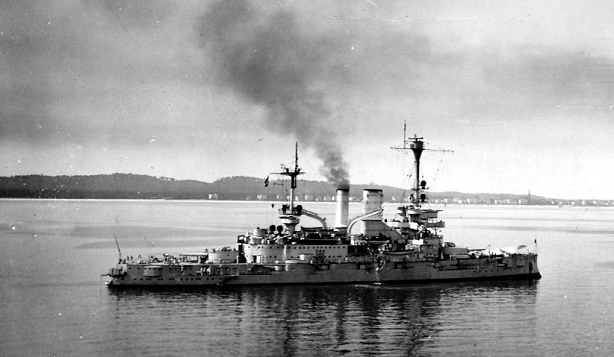
The Schleswig-Holstein
The Schleswig-Holstein was built from 1905-1908. She fought in both world wars. In World War I, she saw action in the Battle of Jutland. One of the few battleships allowed by the Treaty of Versailles for Germany, the Schleswig-Holstein returned to military use in the 1920s. In 1935, she was converted into a training ship. For most of World War II, the Schleswig-Holstein was used for this purpose before being sunk by British bombers in December 1944.
The Schleswig-Holstein fired the first shots of World War II when she took the Westerplatte in Gdansk under fire on the morning of September 1, 1939.
The first Schleswig-Holstein cryptogram
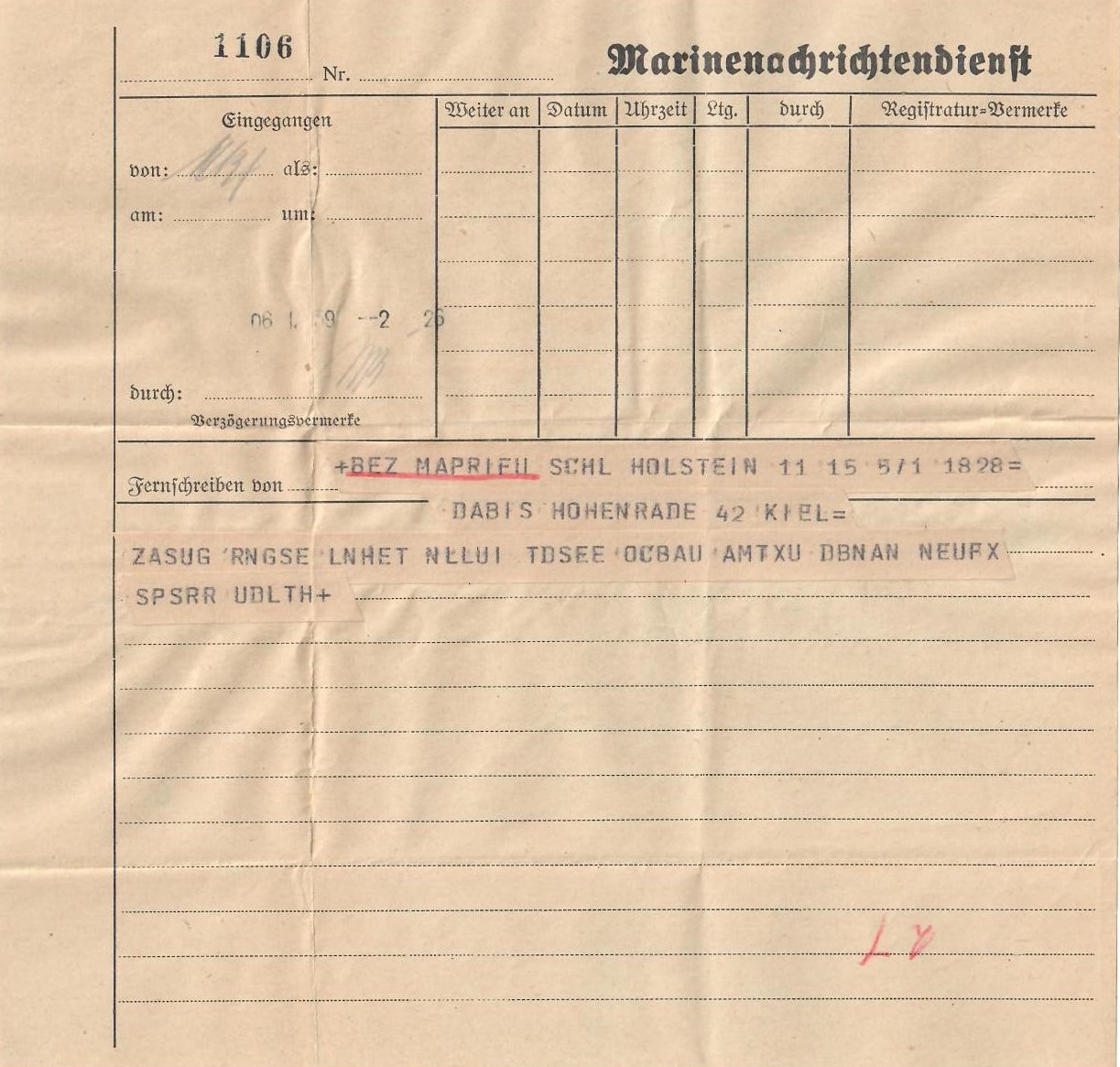
My friend Tobias Schrödel, whom my readers know as a comedy hacker, book author, Stern TV expert, and crypto-book expert, provided me with an interesting document a couple of years ago: an encrypted telex sent from the Schleswig-Holstein to an address in Kiel on January 6, 1939 (see here). Here is a scan of this letter:
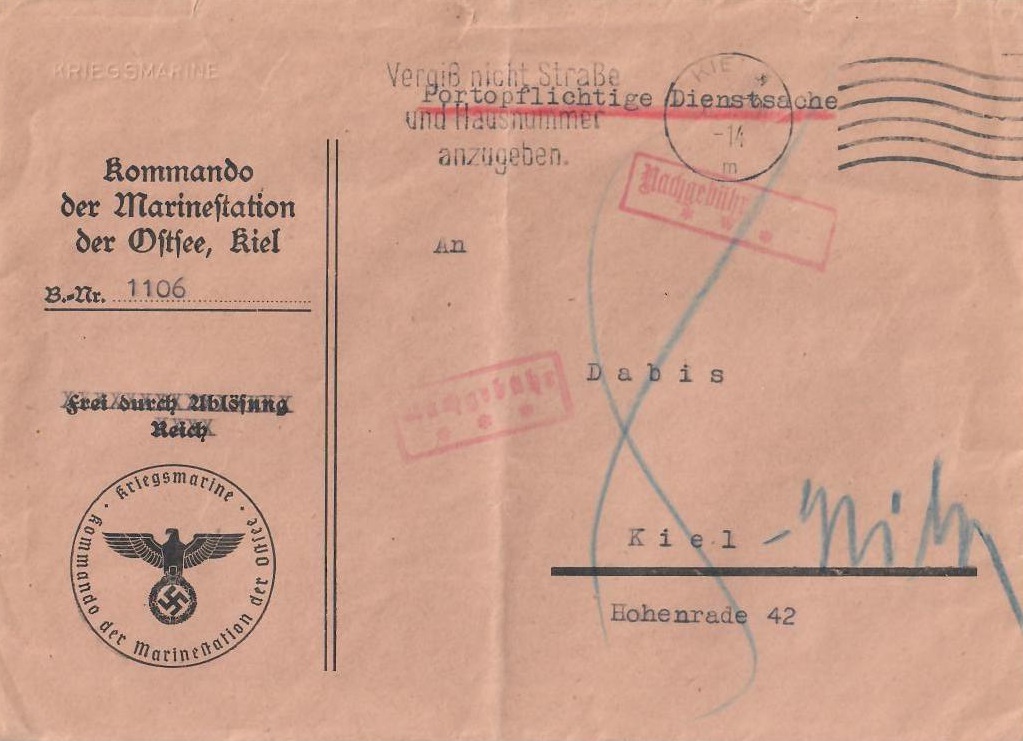
This message (“Schleswig-Holstein cryptogram”) was contained in the following envelope:
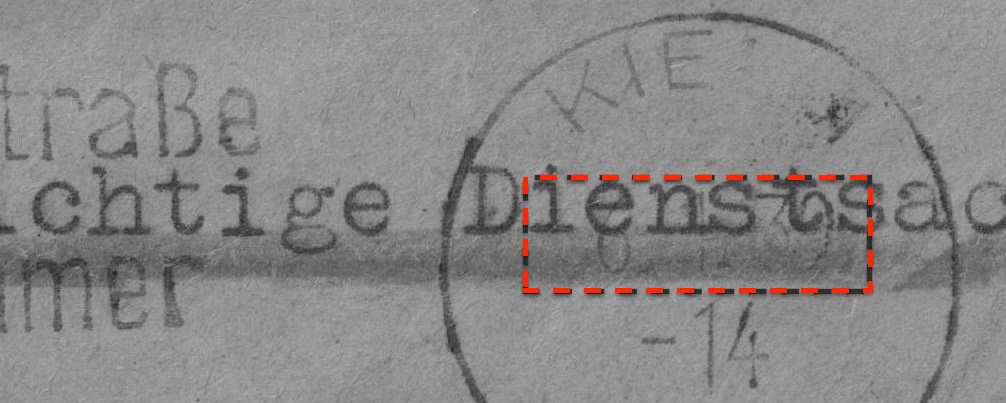
The recipient of this shipment was a person or family named Dabis in Kiel. The surname Dabis is rare in Germany, but does occur in Kiel. The date (January 6, 1939) can be seen on the envelope, which Tobias Schrödel was kind enough to point out to me:
On the back of the letter, the recipient apparently wrote down a shopping list:
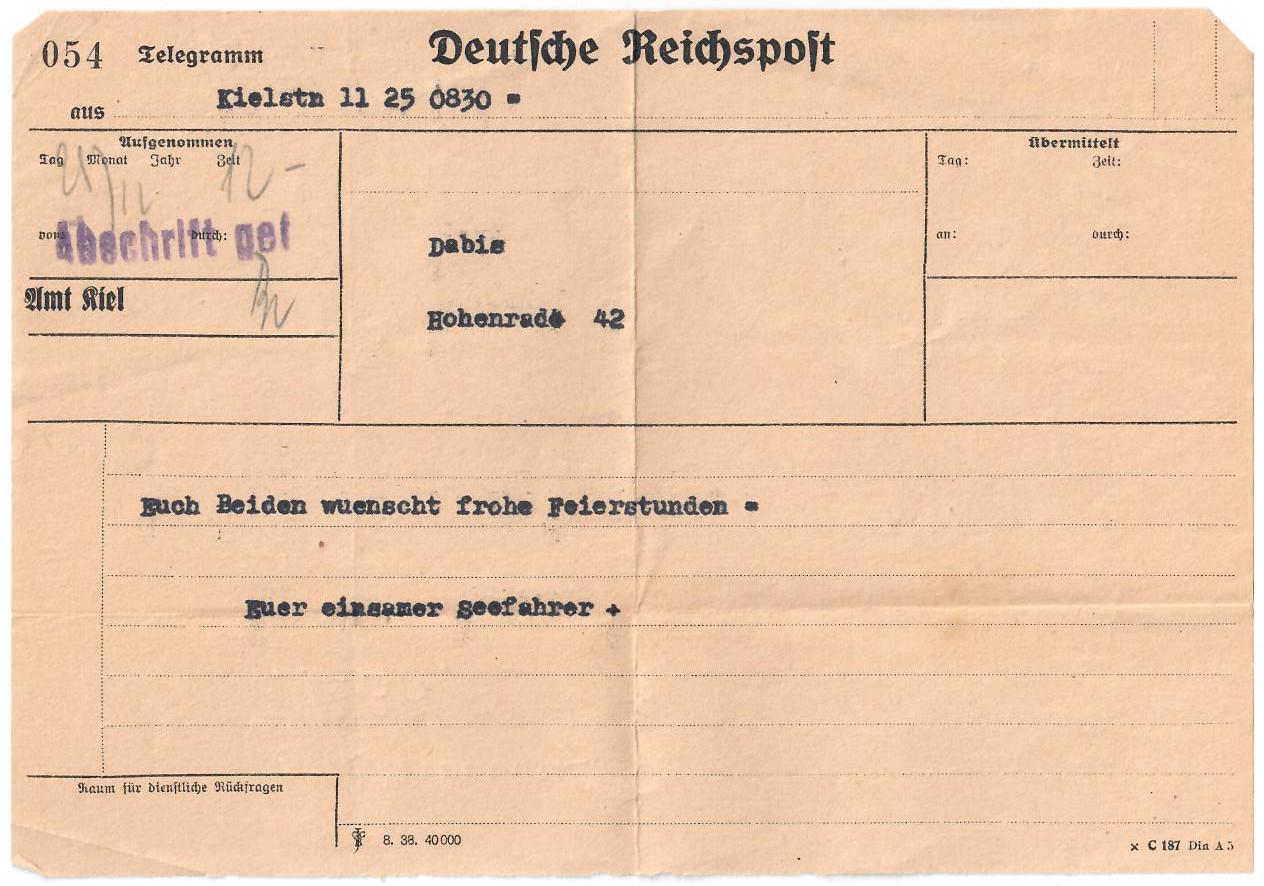
There was another note in the envelope. It was an unencrypted telegram with a Christmas greeting that had already been sent to the same address a few months earlier (on 24.12.1938):
I assume that this telegram was not originally included in the envelope. Presumably, it was merely stored in it by the recipient (as far as I know, telegrams were usually delivered without an envelope).
The Schleswig-Holstein cryptogram can be transcribed as follows:
ZASUG RNGSE LNHET NLLUI TDSEE OCBAU AMTXU DBNAN NEUFX SPSRR UDLTH+
Patrick Hayes
Through the ICCH forum last year, I met Patrick Hayes …
… got to know. Patrick, who runs an interesting website about encryption machines, wrote me the following about himself:
Patrick Hayes is a specialist and collector of cryptologic artefacts. He also brokers cryptologic artefacts linked to the Enigma, T-52 Geheimschreiber and other cipher machines to museums, dealers and collectors across Europe and North America. He is director of the Chiffriermaschine Museum, a virtual crypto history museum available at www.chiffriermaschine.com and is a member of the International Conference of Cryptologic History (ICCH). He is also currently studying History at Durham University, in the UK.
ICCH lectures (they are held in English and transmitted via Zoom) are held every two weeks on Saturdays, by the way. Soon there will be a website for this. The participation links are not yet published on the Internet for security reasons. Everyone is welcome, and participation is free. If you want to participate, please send me an email.
Three more Schleswig-Holstein cryptograms
Patrick Hayes recently sent me three more encrypted messages sent from the Schleswig-Holstein to the Dabis address in Kiel. In addition, he has provided me with further (unencrypted) correspondence from the same source. In total, these are no less than 153 pages – a real treasure, which Patrick describes as follows:
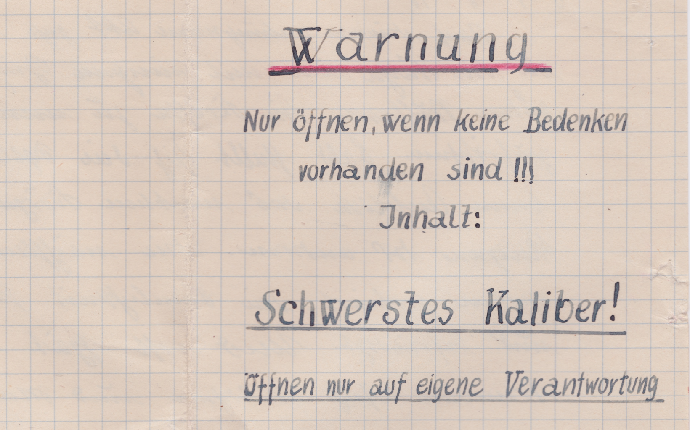
Unfortunately, I can’t publish the entire collection in one blog article. However, all 153 pages are available for download here. The following warning is undoubtedly interesting (p. 6):
Can a reader comment on this? Is this meant ironically?
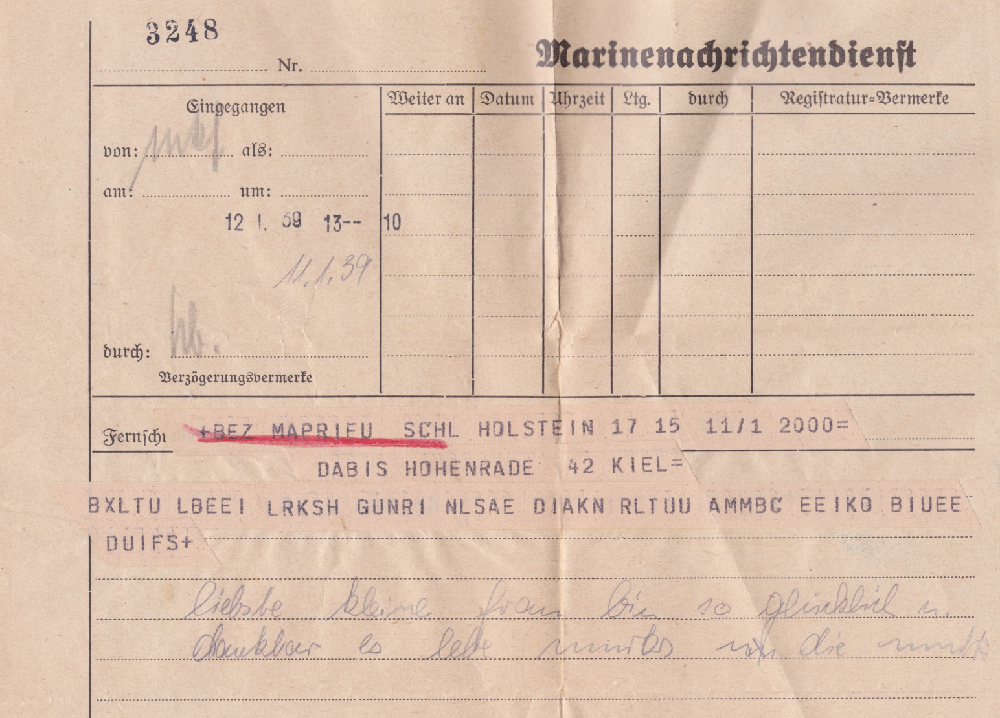
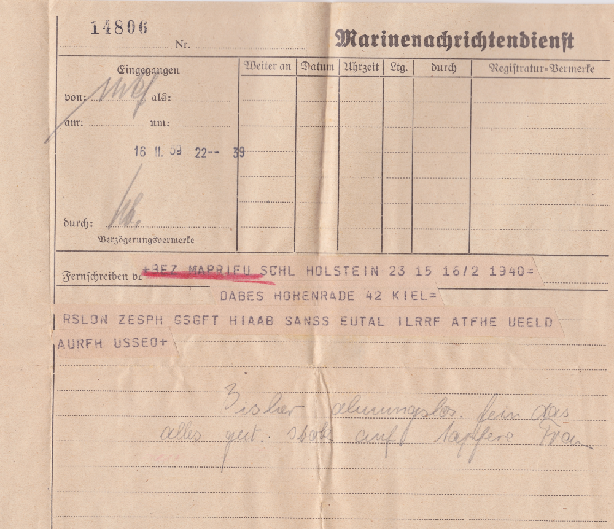
Here is the first encrypted message from Patrick’s trove (i.e. the second Schleswig-Holstein cryptogram):
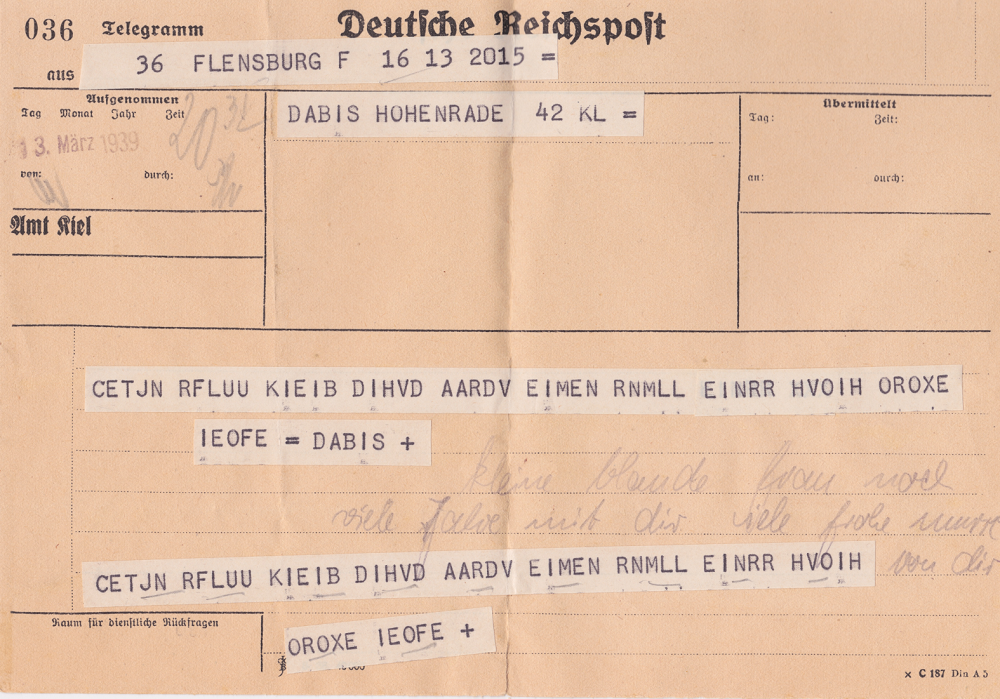
Schleswig-Holstein cryptogram number 3 follows:
And finally, the last ciphertext in this series so far:
Does anyone manage to decipher these four cryptograms?
After my first article on the subject, there was an extensive and very interesting discussion. Jim Gillogly, an excellent codebreaker thought that a transposition cipher might have been used. On the other hand, a professional method – such as a codebook or an encryption machine – seems rather unlikely.
Thanks again to Tobias Schrödel and Patrick Hayes for this exciting cryptogram series!
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: An encrypted letter from World War 2



Letzte Kommentare