David Vierra is the new bearer of the Friedman Ring
David Vierra has solved the challenge of Matthew Brown. He is now the new bearer of the Friedman ring.
The first person to solve the current crypto puzzle creates the next one. The Friedman Ring works according to this simple principle. This is a game named after cryptologists William and Elizebeth Friedman and inspired by the Iffland Ring (an award for actors).
All previous prize winners can be found on this website.
Meanwhile, the seventh round of the game has ended. The puzzle came from Matthew Brown. David Vierra was the first to solve it, making him the new bearer of the Friedman Ring. Congratulations to all who participated! And thanks also to the many others who posted comments.
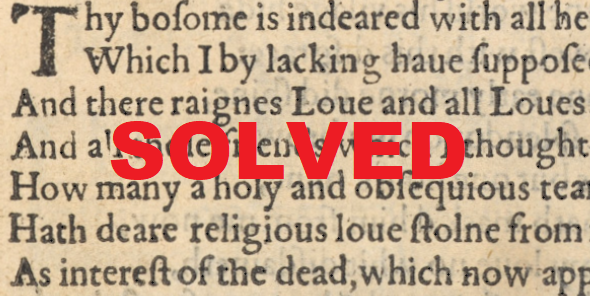
Matthew’s Challenge
Matthew had created the following challenge, which consists of two parts:
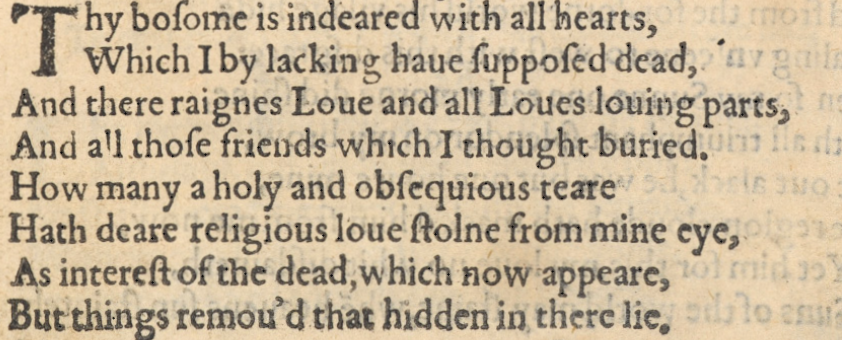
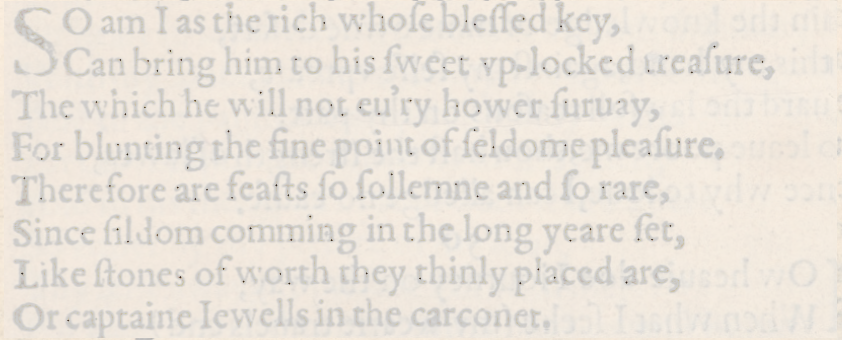
This is the second part:
The two texts are by Shakespeare. Matthew did not provide any further information. As you can see, there is no encryption to be seen at first. So it is a steganographic code.
On the way to the solution
Matthew’s challenge has generated an enormous amount of interest. To date, 206 comments have been posted on the related Cipherbrain article. In the almost ten-year history of this blog, there has been only one post with more comments (it was an article about Cicada 3301). Contributors to Matthews Challenge were Bernd Adameit, Norbert Biermann, Thomas Bosbach, Bill Briere, Peter Bull, Bob Dovenberg, Magnus Ekhall, Thomas Ernst, Etsch, Gerd Hechtfischer, Nils Kopal, Tom Larsen, Marc, Narga, Rizzie, David Scheers, TWO and YefimShiffrin. Apparently there were discussions about the puzzle on Discord as well. Perhaps a reader can send me a link or a screenshot.
Finally, the correct solution was found by David Vierra. David has commented on Cipherbrain many times, but I have never met him in person and did not exchange mails with him before this challenge. After his success, I contacted him and he provided me with some information about himself.
David lives in Hawaii (Big Island) and is known on github as well as Reddit’s r/codes as codewarrior0. He was not interested in cryptography until he came across a
cipher puzzle hidden in the computer game “Noita”. I blogged about this puzzle recently. To solve the puzzle, David read books on code breaking, from William Friedman’s works to George Lasry’s book on heuristic search algorithms. I hope that my book, Codebreaking: A Practical Guide, was included. Unfortunately, David did not manage to solve the Noita cryptograms, although no one else has managed to do so either.
The solution
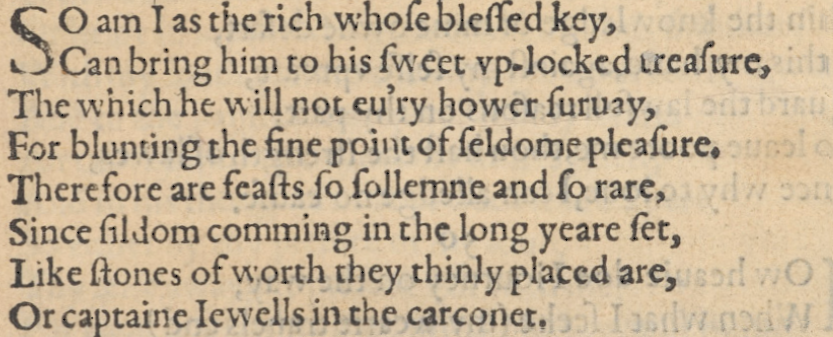
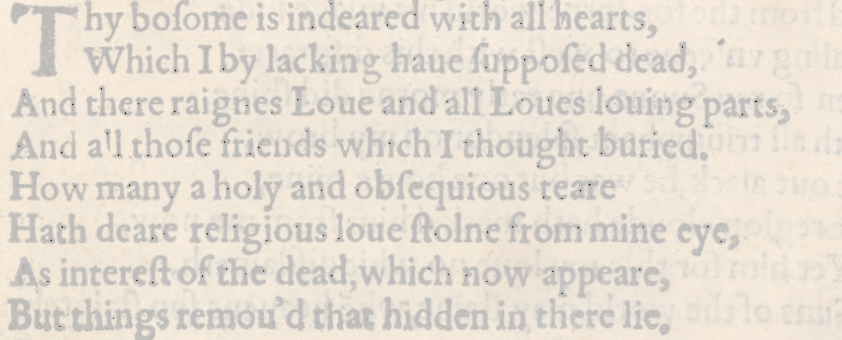
If you brighten up Matthew’s pictures, you can see numerous small dots in them. The following illustrations were made by Norberts Biermann:
The dots are used to mark letters of the text. In this sense, there are two types of letters: marked and unmarked. As early as the 16th century, Francis Bacon described how two types of letters can be used to represent an alphabet consisting of groups of five:
As an example, let’s look at the first five letters in Mathew’s first Shakespeare text. Only the fourth letter is marked, so the pattern is AAABA. This corresponds to the C in Bacon’s table. All in all, we get the following cryptogram for the first text with Bacon’s table (thanks to Norbert for the decoding):
NLRHHCTVNNSESITISIESAWAHCOSHNGETOAROVILEPETRANSHPT
Here is the result for the second text:
LOSBKTAEEOEAAEGRAHDUEHBNEDNENSEEIFYMYOKCESBMANTSNN
Matthew confirmed that the bacon cipher approach was correct. However, he had made two errors in the first text. Here is the corrected version:
NLRHHCTVNNSESITISIESAEAHCOSENGETOAROVILEPETRANSHPT
LOSBKTAEEOEAAEGRAHDUEHBNEDNENSEEIFYMYOKCESBMANTSNN
The letter frequencies speak for a transposition cipher. But what is the correct order of the letters? David Vierra finally found the right approach. Since both texts are the same length, he suspected that the same rearrangement was used in each case. He then found the correct order by trial and error, taking advantage of the fact that for each rearrangement he tried, both texts had to make sense. This technique is also called multiple anagramming and is described in my book “Codebreaking: A Practical Guide”. This resulted in the following solution (I have inserted spaces for clarity):
EVEN THE STRONGEST TRANSPOSITION CIPHERS HAVE AN ACHILLES
HEEL AND ANY MESSAGES FOUND TO BE IN THE SAME KEY CAN BE BROKEN
If you number the letters in plain text (starting with zero), the rearrangement (i.e. the key) for both texts is as follows: 21 7 30 0 6 23 18 16 49 34 35 8 29 41 12 14 31 2 33 9 19 48 25 46 37 42 13 32 45 5 17 40 47 11 43 10 4 20 36 39 44 28 22 24 3 15 1 38 27 26.
As David reported, he found the solution by manual trial and error, guessing that the words TRANSPOSITION CIPHER occur in the text. Computer programs that solve transpositions did not help him. However, he created some scripts that helped with multiple anagramming.
The next round is coming for sure
Once again, I am thrilled with my blog readers. Matthew Brown created a great puzzle that David Vierra did an impressive job of solving. Of course, he benefited here from the preliminary work of other readers who also did great things. Thanks to all of them!
Since Cipherbrain will be discontinued at the end of the year, I can’t say yet what will happen with the Friedman ring. However, I assume that a solution will be found.
If you want to add a comment, you need to add it to the German version here.
Follow @KlausSchmeh
Further reading: Ein kryptologischer Cold Case: Die BND-Challenges von 2014
Linkedin: https://www.linkedin.com/groups/13501820
Facebook: https://www.facebook.com/groups/763282653806483/


Letzte Kommentare