
Die Plattform Scienceblogs.de wird leider Ende 2022 eingestellt. Dadurch verliert auch Cipherbrain seine Heimat. Da bisher keine Nachfolgelösung in Sicht ist, wird dieser Blog erst einmal nicht weitergeführt werden.
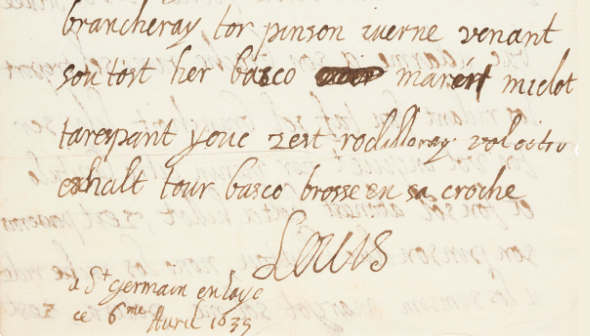
Im Jahr 1635 verschickte der französische König Ludwig XIII. einen verschlüsselten Brief an einen unbekannten Empfänger. Die Lösung ist nicht bekannt.
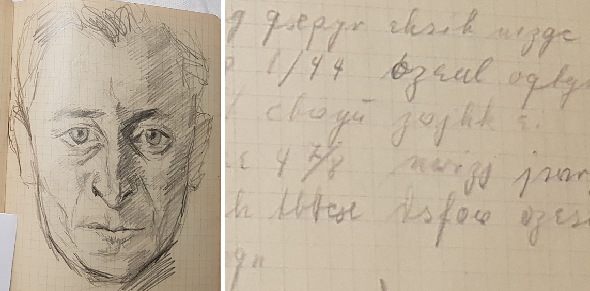
Der deutsche Maler Göbel hinterließ ein Notizbuch mit etwa zehn möglicherweise verschlüsselten Passagen. Kann ein Leser diese Krypto-Rätsel lösen?
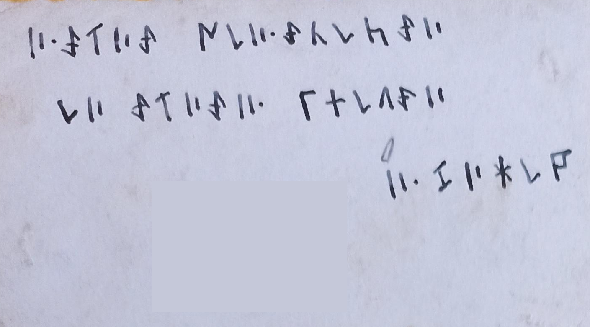
Zwei Wochen vor einem Suizidversuch verfasste eine jugendliche Person eine verschlüsselte Nachricht. Kann ein Leser diese lösen? Oder ist das Ganze nur ein Scherz?
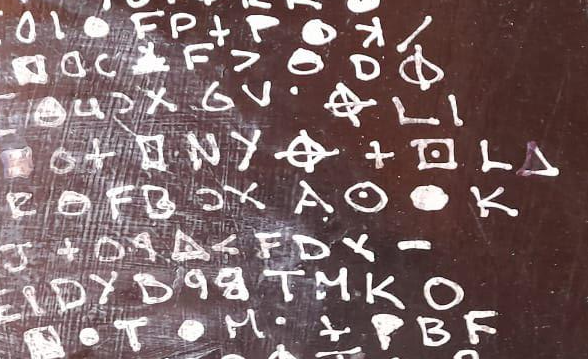
Ein Soldat beschriftete im Zweiten Weltkrieg Fotos in verschlüsselter Form. Kann ein Leser diese Kryptogramme lösen?
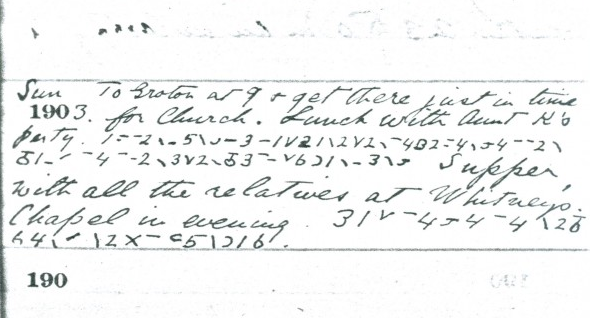
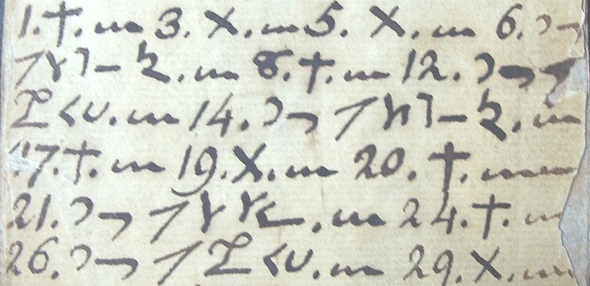
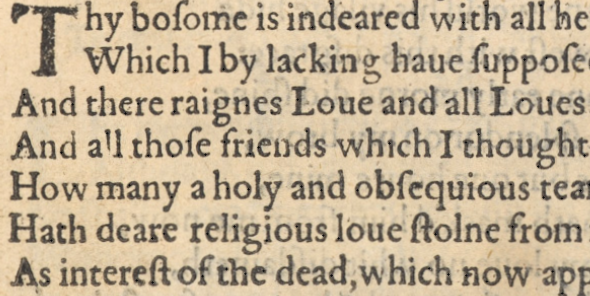
Heute geht es um einen prominenten und um einen unbekannten Tagebuchschreiber aus den USA. Beide nutzten Verschlüsselung.
Vor 200 Jahren führte eine unbekannte Person in den USA ein verschlüsseltes Tagebuch. Meines Wissens ist dieses bisher ungelöst.
In vier Wochen findet eine Online-Konferenz zum Voynich-Manuskript statt. Einige alte Bekannte werden als Redner dabei sein.
Vor vier Monaten hat Matthew Brown die Challenge von Norbert Biermann gelöst und ist damit der aktuelle Träger des Friedman-Rings. Heute stelle ich Matthews neue Challenge vor. Wer sie löst, wird sein Nachfolger.
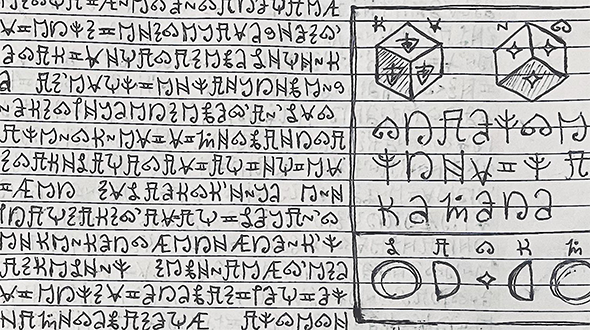
Auf Reddit haben mehrere Nutzer Fotos von ihren verschlüsselten Tagebüchern veröffentlicht. Kann jemand die Verschlüsselungen knacken?


Letzte Kommentare